That step created an entirely new layer of the internet where anonymity applied on both sides. Over the years, onion services moved from the short, insecure v2 addresses to the more secure v3 standard used today. This guide helps readers understand .onion addresses, their role on the internet, and how to explore them safely. It is not a clickable directory of hidden services, and it does not promote unsafe or illegal activity. The goal is to explain how these domains function, highlight their legitimate uses, and give practical advice for staying secure.

The Rise Of 2024 Darknet Marketplaces
The integration of advanced encryption technologies and decentralized systems ensures that transactions remain confidential, while user feedback mechanisms enhance trust among participants. The combination of technological advancements and user-centric design positions these markets as a reliable and secure option for drug trade in 2025. Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web. A VPN encrypts the data traffic and keeps your activities private on the dark web. It also masks your IP address, making it difficult for government agencies to monitor or track your activities.
How Darknet Market Lists Enhance Secure Drug Trade
Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P.
Missing The Wider Landscape Of Digital Harms
If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last.

Why CISOs Should Bet On Startups In Today’s Cybersecurity Market

Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous. The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. In 2024, the popularity of black traffic schemes on underground markets remained constant. Black traffic dealers have maintained their operations by promoting malicious landing pages through deceptive ads.

Trends Shaping Dark Web Activity In 2025
- Additionally, threat actors appear to be increasingly using multiple programming languages.
- The use of cryptocurrencies such as Bitcoin and Monero remains central to these platforms, ensuring anonymous transactions and reducing the risk of financial tracking.
- The social media giant is also aware of the many attempts by repressive regimes to restrict its access.
- Keep Tor Browser updated, block unnecessary scripts, and avoid suspicious downloads.
But it also created the foundation for what would become “hidden services” — websites you couldn’t find on Google, accessible only through special browsers. One of the key factors driving the growth of these markets is the diversity of products available. From pharmaceuticals to recreational substances, users can find a wide range of options tailored to their needs.
Understanding The Layers Of The Web: Surface, Deep, And Dark
These platforms rely on advanced encryption and decentralized systems to ensure anonymity and reliability for both buyers and sellers. In 2025, dark web markets continue to grow more sophisticated, leveraging cryptocurrency as their backbone for financial transactions. These hidden digital spaces host a variety of illegal and illicit activities, from drug trafficking and weapons sales to data breaches and financial fraud. The decentralized, pseudonymous nature of cryptocurrencies has provided a strong foundation for these underground markets to expand, adapt, and resist law enforcement pressure. In 2025, the darknet drug trade continues to evolve, with markets expanding their offerings to include a wider range of products.

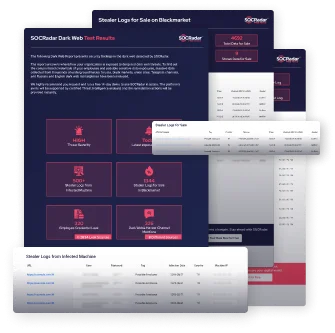
Reports indicate that more than 60% of SMBs targeted by cyberattacks shut down within six months, often due to exposed credentials or financial fraud linked to dark web activity. Cybercriminals are leveraging artificial intelligence to automate attacks, refine phishing strategies, and exploit security vulnerabilities faster than businesses can respond. A robust cybersecurity risk assessment is no longer optional—it is a critical necessity for businesses to safeguard sensitive data and financial assets.
The Future Of The Dark Web And Cybersecurity In 2025 & Beyond
In just two years, Russian Market experienced a 670% surge in stolen log inventory, reaching over five million by early 2023. Criminals now purchase ready-to-use malware kits, phishing templates, and ransomware programs. These tools come with user manuals and customer support, enabling even non-technical actors to conduct complex cyberattacks. Despite the churn, the top five platforms dominate, handling roughly 72% of all transactions.
While authorities have failed to shut it down, the forum hasn’t, fortunately, witnessed easy sailing either. For instance, in January this year, it was the target of Operation Talent, the law enforcement initiative that was coordinated by the FBI and international agencies. It’s an operation that led to Cracked losing the original domain, but didn’t disappear – it simply moved to the new address. For certain groups, dark and deep web (DDW) forums exist for anonymous chatting and discussion on sensitive topics like government censorship and more. Discover crucial dark web statistics, trends, and emerging threats to stay ahead of cybercrime in this fast evolving digital era.
- Bitcoin remains the primary currency, offering anonymity and ease of use, though some markets are beginning to integrate alternative cryptocurrencies for added flexibility.
- The most famous example is Silk Road, launched in 2011 as a marketplace for drugs and digital goods.
- The deep web refers to all online content not indexed by search engines, such as virtual private networks and internal business systems.
- His articles have appeared in many respected technology publications.
- In 2024, we observed a surge in the activity of “drainers” across dark markets.
- Smaller forums also exist, focusing on security discussions and activism.
The Rise Of Secure And Reliable Drug Trade On Darknet In 2025
But those of us who have studied this space for years weren’t surprised. But shutdowns like this have become a recurring feature of the dark web. Exploring the hidden web safely requires more than a single guide. Readers who want to go deeper should rely on trusted resources that focus on privacy, security, and ethical use. These materials not only expand knowledge but also help avoid the misinformation that often surrounds the dark web.
Its 25,000+ users and 3,000+ vendors trust its unmatched escrow and scale. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check.
Some onion domains attempt to install harmful software the moment they load. Malware can steal passwords, log keystrokes, or give attackers full control. Look for signs of credibility, such as frequent updates, strong community references, and transparent moderation. The best approach is to confirm any onion address with multiple trusted sources before visiting.
This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely. This adds extra protection since opening Tor itself encrypts your traffic. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address.



