Advanced encryption technologies support anonymity, while cryptocurrencies ensure that financial trails remain difficult to follow. The site’s...
bitcoin
The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. Established...
This process starts with a curated list of seed addresses sourced from platforms like Ahmia.fi. The crawler...
Another option is to use anonymous payment methods, such as prepaid debit cards or gift cards. These...
It is important to note that while regulation can help address dark web Bitcoin activities, it should...
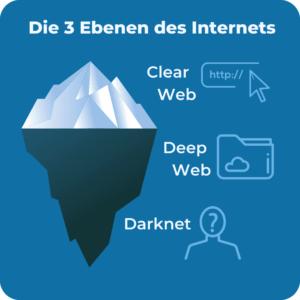
Once Tor became widely available, people began using it to host websites, giving rise to what we...
It is known for its illicit activities, including the buying and selling of illegal goods and services....
People brave enough to access the dark web mainly use Tor and I2P. As for layout and...
As described by IRS Criminal Investigation Chief Guy Ficco, investigators “cracked the code of so-called ‘safe spaces’”...
For instance, cybercriminals can buy credit card details with a $5,000 balance for just $110. Today’s cybercriminals...