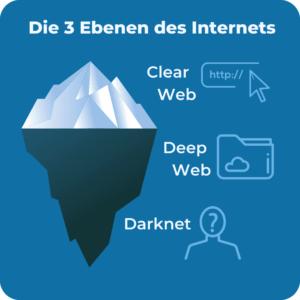
Named entity recognition in cyber threat intelligence using transformer-based models is another example that can be used...
illegal
Malicious websites, compromised Tor nodes, or accidental downloads can expose your device to malware or hackers. It’s...
However, engaging in criminal activities on the dark web can lead to serious legal consequences. While Bitcoin...
It’s not the kind of place you’d imagine an investigation into black market Ozempic would lead. To...