If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client.
ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. In most cases, whistleblowers have sensitive information about the government or a company. They can be easily traced and even prosecuted if they share the information on the surface web.
Microsoft Warns About New Variant Of XCSSET Malware On MacOS
The Onion Router (Tor) also made the technology available in 2002. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address.
Subscribe To The Blog Newsletter
“Over the years some markets … developed a robust catalog of illicit services like money laundering, fiat offramping, and products that enable cyber-criminal activities like ransomware and malware attacks. One such sophisticated darknet market, Hydra, offered all that and more,” Chainalysis explained. Nemesis Market is a relatively new wallet-less shop on the dark web where you don’t need to deposit any amount in your wallet before buying products from here. The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them. You can see all the product categories the marketplace deals with on the homepage. Like other marketplaces, it also requires registration for new users and accepts payments in Monero.
DeepDotWeb – A Major Gateway To Darknet Marketplaces Shut Down
- The quantity, price, and characteristics of the product are all provided.
- Browsers with the appropriate proxy can reach these sites, but others can’t.
- Privacy advocates frown upon it because of the way it harvests data and profiles users.
- People mostly use it for covert communication, anonymous tips submission, and stuff like that.
Hidden Facebook is hardly the only social media client on the dark web. People mostly use it for covert communication, anonymous tips submission, and stuff like that. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows.
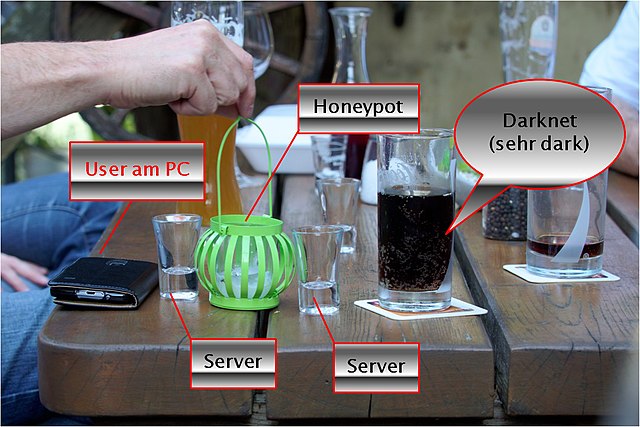
The Three Internets
In this article, we will provide a comprehensive guide to dark market links, including what they are, how they work, and how to access them safely. Dark markets are online platforms on the darknet where illegal goods and services are traded. You can find drugs, weapons, stolen data, and counterfeit documents on these marketplaces. They operate similarly to regular e-commerce sites but use cryptocurrencies for transactions. Most dark markets have user review systems and vendor ratings to establish trust. Law enforcement regularly shuts down these markets, but new ones continuously emerge.
Bohemia Market Links
That alone might already raise suspicion and place you under special surveillance. Some reports say the FBI will simply label you a “criminal” once they’re aware you’re using the Tor browser. Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. It’s impossible to access the dark web with a regular browser like Chrome or Safari. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy.

Popular Dark Web Links & Websites
I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. Think of Tor as a regular browser like Firefox, Google, or Safari. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed.
Black markets enable the morally libertine to profit handsomely in Bitcoin. The site was raided and shut down by the FBI in 2013, but the idea of an anonymous, encrypted black market spread rapidly. What differentiates the so-called Dark Web is the method by which sites are accessed. The Dark Web, or darknet, is a network of sites with encrypted content, accessible only with a secure suite of secure-browsing tools, like Tor.

What Are Dark Market Links?
The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. You can either sell or buy goods on the dark web, but both present difficulties.
Hidden Cyber Risks Of Generative Artificial Intelligence
In order to avoid censorship of their content, they’ve created a .onion site to ensure it’s accessible for all. ProPublica was the first online publication to win a Pulitzer prize. They were also the first to host a .onion site to make their content accessible to everyone everywhere, regardless of censorship or anti-journalist laws in certain countries. In successful cases, law enforcement can combine this intelligence with other investigative techniques to seize the online infrastructure and residual virtual currency, like in the case of the Silk Road seizure. In an economy where the demand—drug-addicted users—remains constant or growing, that’s only to be expected. So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers.
Most dark web links are hosted on “.onion” domains due to the sensitive nature of the businesses or services they host. Tor websites may provide secure access to cryptocurrency wallets and anonymous email clients, and they’re also used to access black market sites. Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. To purchase illicit goods or services, users deposit cryptocurrency into an escrow system or directly to the seller, and the cryptocurrency is held until the buyer confirms the satisfaction of the transaction. These markets are hidden from search engines and require special software, such as the Tor browser, to access.

Ruheni explains complicated technical concepts clearly and simply. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.