In January 2021, after a sustained international law enforcement campaign led by the FBI and supported by Interpol, Joker’s Stash closed operations permanently. Prior to its closure, Joker’s Stash hosted over 40 million stolen credit card records and generated hundreds of millions of dollars in illicit revenue. In the world of cybercrime, darknet carding sites have emerged as a significant threat to individuals and businesses alike. These sites, which operate on the dark web, are used to buy and sell stolen credit card information, often obtained through data breaches or phishing scams. Darknet carding sites are websites that operate on the darknet and are used to buy and sell stolen credit card information. These sites are often used by cybercriminals to monetize data breaches and other forms of cybercrime.
Get Same Day Money Transfer Now!!!
- This ensures credit reporting agencies will not provide your credit report if anyone tries to open a new loan or credit card account in your name.6.
- The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is.
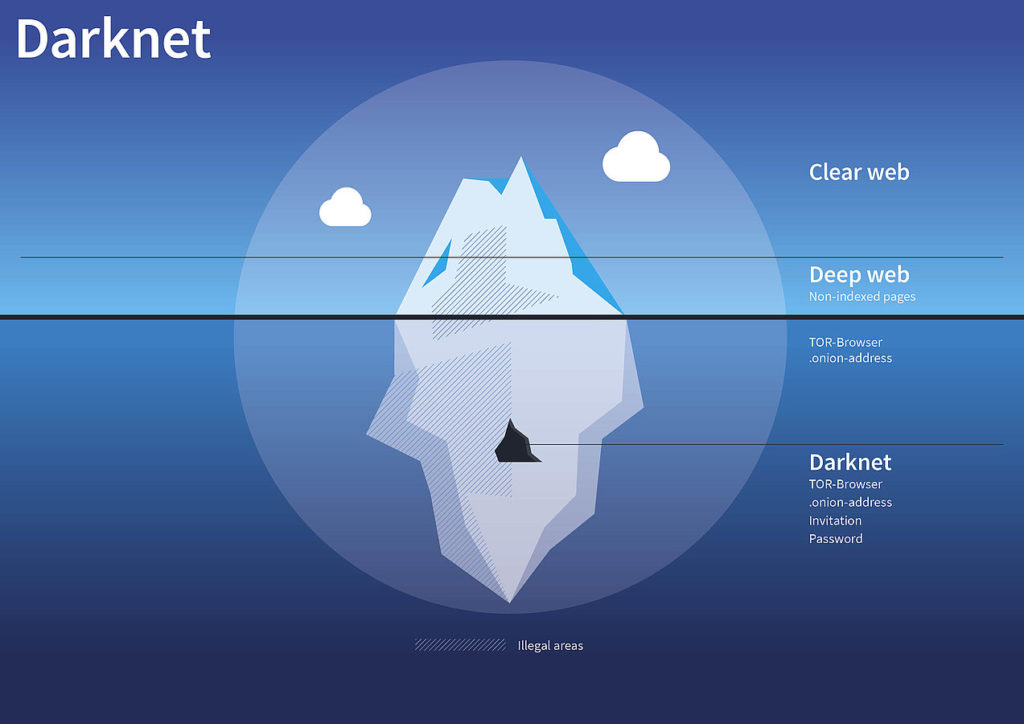
- These sites operate on the dark web, an area of the internet not indexed by conventional search engines and requires specific software, configurations, or authorization to access.
- Thankfully, there are effective measures that keep you secure on the dark web and ensure you remain protected and anonymous while accessing .onion sites.
- Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages.
- Transactions can be quickly flagged or blocked, making fraud attempts risky and unreliable.
Like regular browsers with domain names, the Tor browser also has its own domain designation. These “onion” sites are only accessible on the dark web and bear the “.onion” domain at the end of the URL. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing.
How To Access These Deep Web Carding Forums “safely”?
It’s great for people who live in or travel through restrictive countries to securely access and use image hosting and sharing services, which might be unavailable. There’s even an option to set a timer on your most sensitive messages so they disappear after a set time period. ProPublica has a clearnet site, but its dark web version won’t see your IP address, so you get better privacy. You can also use its .onion link via the Tor network to access the site in restrictive countries, where it might be unavailable. The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites.
Step 1: Obtaining The Stolen Credit Card Data
- I’ve seen cases where security teams identified compromised card data from their institution appearing on the dark web weeks before they traced the actual breach point.
- The market sells credit card information to users occasionally shares free credit card dumps (as seen below).
- Check out these best onion sites to access the dark web securely and anonymously.
- For an added layer of protection, consider purchasing a virtual private network, or VPN.
- However, please note this article is for research and educational purposes only.
Usually, criminals sell access to exploits and stolen data, but increasingly sites such as 0day.today are releasing more free material, from exploits to data dumps. This is a popular dark web site that peddles software exploits which hackers can use to break into your computer or network. Using a reliable VPN with Tor provides a way to improve security when accessing dark web links. The VPN encrypts your traffic before it enters the Tor network, preventing your ISP from seeing that you’re using Tor. This double encryption also protects against compromised Tor entry nodes that could potentially monitor your activity.
CC Quality Vendor Forum (Offline)
Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. Cryptocurrencies such as Bitcoin have been the dark web currency even before they became available to the general public. Right now, you can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies. Formerly known as Archive.is, it is one of the best onion sites on the dark web. While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The social media giant is also aware of the many attempts by repressive regimes to restrict its access.
It’s a good idea not to download anything from sites or sources you don’t know and trust. People generally buy these accounts due to content restrictions on their own accounts. The hacked accounts may be from country that has a bigger streaming site library than their own. This is kinda weird because people can use a VPN to unblock streaming sites.

The Hidden Wiki
This ensures credit reporting agencies will not provide your credit report if anyone tries to open a new loan or credit card account in your name.6. Add additional challenges for financial accounts and mobile providers wherever possible. Free and paid tutorials on the dark web teach fledgling criminals how to use stolen credit cards. The rise of verified market lists has further simplified access to these platforms, ensuring users can connect to legitimate and secure marketplaces without the risk of phishing or scams. Additionally, the growing popularity of darknet forums and magazines has created a robust ecosystem where users can share reviews, discuss trends, and stay updated on new market links. These stolen cards have value because they can be used to purchase expensive items or gift cards, which can then be resold for cash.
Flare, for example, enables you to automatically scan the clear & dark web for any leaked or stolen account credentials. By doing this, you can find your credentials for sale on the dark web and secure them before they are exploited. Since then, BidenCash has continued to operate using the “dumping” method.
Understanding Darknet Carding Sites

Federal convictions for credit card fraud can result in fines of up to $250,000 and prison sentences ranging from several months to over 20 years, depending on the scale and severity of the crime. For example, in 2022, an Ohio man was sentenced to 10 years in federal prison for his role in a carding scheme involving over $1 million in fraudulent transactions. In 2018, the FBI successfully concluded Operation Card Shop, targeting the notorious carding forums Infraud Organization and Cardplanet. Infraud Organization alone was responsible for losses exceeding $530 million globally. Following extensive undercover operations and coordinated international raids, 36 individuals across several countries were indicted, resulting in numerous arrests.
One of the key features of top-tier darknet markets is their use of Tor networks, which provide users with a high level of anonymity. By routing traffic through multiple nodes, Tor ensures that IP addresses are concealed, reducing the risk of exposure. Additionally, many markets now implement multi-signature escrow systems, which protect both parties by holding funds until the transaction is confirmed as successful. Closures and seizures of carding sites in 2022 have so far accounted for almost 50% of sales in the dark web stolen credit card market.
Sellers may not deliver the stolen credit card information as promised, or the information may be outdated or incomplete. It is important to remember that there are no guarantees when using darknet carding sites, and you are taking a significant risk by using them. In a more recent development, on February 19, 2025, B1ack’s Stash escalated its operations by claiming to leak an additional 4 million stolen credit card details for free.
How Are Credit Card Data Stolen?
Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale.
But in terms of defense, companies benefit from large resources that can really make a dent in their earnings. For instance, machine learning has shown time and time again that advanced technology can detect patterns that fraudsters aren’t aware of. In short, you can’t make them go away, but you can surely make their life harder. Some alleged services like the professional “hitmen” may just be scams designed to profit from willing customers. Reports have suggested the dark web offers many illegal services, from paid assassinations to trafficking for sex and weapons.