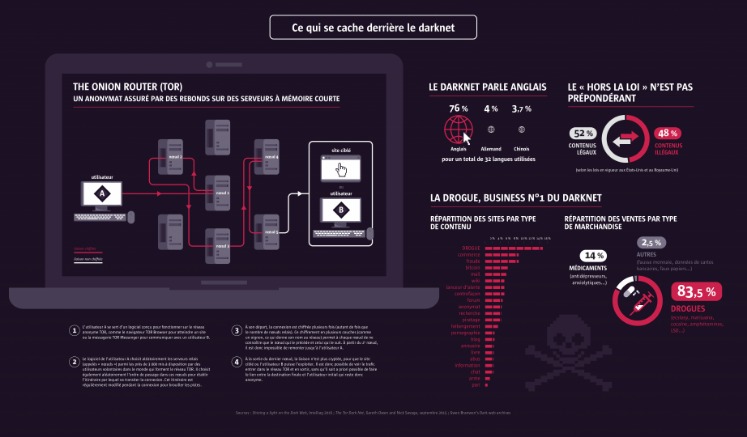
Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites. When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. Each server adds a layer of encryption, and this layered system is what lends The Onion Router its name. This is also why the sites on the dark web are called Tor links. Within the mega darknet, there is a hierarchy of services and websites that can only be accessed via invitations or after complex authentication processes. This structure ensures that only trustworthy members have access to certain areas, which further increases the security aspect and promotes the formation of closed communities.
Secure Drop
Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs. It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities. Through the dark web, users in places of high censorship can also access information and news. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017. You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it.
Due to the value of the private data that is stored on the deep web, it is vital that it is always secured extremely well using encryption. Tor browser is named after “The Onion Router” protocol that powers the dark web. As mentioned, Tor servers are completely concealed from regular internet browsers.
What Is Archetyp Market?
Ross Ulbricht, the creator of Silk Road, was arrested on suspicion of hiring a hitman to kill six people, but the charges were later dropped. Mostly on the dark web, financial transactions happen via cryptocurrencies such as Bitcoin, making it possible for parties to do business anonymously. The open web makes up less than 4-5% of the internet, which is just the tip of the iceberg of the entire internet. Think of it as an iceberg, with only a tiny part visible above the surface. If you dig deeper, you’ll discover the mysterious world of the deep web and, for the brave ones, the foreboding dark web.
Bitcoin Wallets

While it’s true that some corners harbor illegal activities, it also provides a platform for whistleblowers, journalists, activists, and everyday users seeking privacy and freedom from censorship. The dark web contains content that’s only accessible through networks like Tor. Sites in the dark web have .onion as their domain in their URLs.
Tor-over-VPN Vs VPN-over-Tor: The Right Order
While it’s generally safe to use, dark web activity can be detected at the entry and exit nodes of the Tor network. You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions. If you plan to purchase on a dark net marketplace or dark web commerce sites, you’ll need to create a fake identity. Remember only to make purchases using digital currencies and never provide any online banking login details.
Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays. Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal. There are some websites you can absolutely get in legal trouble for even visiting, so proceed with the utmost caution. In this guide, we’ll show you what you need to know about how to access the dark web and how to keep yourself safe while you use it. This requires your connection to go through multiple nodes and relays, which will slow down browsing on Tor.
Facebook Onion Site
- Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences.
- As your traffic passes through Tor, it’s encrypted and bounced between at least three relay points, known as nodes.
- There are thousands of websites on the dark web, many—but not all—of which are illicit marketplaces selling stolen personal data.
- There’s also MultiHop that boosts your encryption, along with MACE which blocks tracking.
This is just the first but also very important step to go to the dark web anonymously. We can say the same about private networks belonging to companies and other entities. Some hospitals even have classified medical records you can’t access just like that.
Protect Your Personal Data
Successfully navigating this hidden world requires preparation, vigilance, and a thorough understanding of both the technical and ethical challenges at play. From choosing the right networks and privacy tools to avoiding scams and malicious software, every step you take should be guided by caution and informed judgment. Navigating the Dark Web can be a complex endeavor, but you don’t have to do it alone.
How To Minimize Risks:
Whether this is a Linkedin profile, Facebook, social media, or any community involvement, chances are that you already have some online presence. While Tor is a powerful tool for defending your privacy, it isn’t the only one. The term is very general, as there are actually a number of ‘darknets’ available such as ‘Freenet’ and ‘I2P’ but the TOR network has become the most popular. Most corporate and public sites work hard to make sure that these web crawlers can easily find them.
Stand Up For Privacy And Freedom Online

The Tor Browser uses several layers of encryption to strengthen your anonymity and has integrated the DuckDuckGo search engine, a system that makes a point of not saving or logging your search queries. As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet. This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources. No longer restricted to dial-up, many of us now consider access to a stable high-speed internet connection a critical element of our daily lives. We pay our bills online, check our bank statements, communicate via email, find information, and maintain a presence on social media.
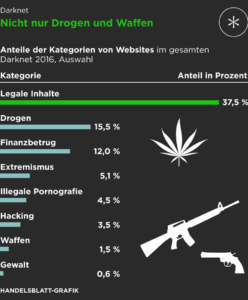
Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites. We also recommend that you use a VPN for Tor, as this will ensure that you add an extra layer of privacy to your connection to Tor. Head over to our page on how to safely access the dark web for some top security tip. Most people have heard of the dark web and the illicit marketplaces available on it. Those marketplaces – and the stories surrounding them – can make the dark web seem like a hive of criminality.
You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers. There are many legitimate uses for dark web services and communication. To access those specific darknet networks, you will need to use the specific browsers developed for them. However, bear in mind that they are often less user-friendly than Tor (which makes accessing the dark web easy). The deep web refers to any part of the internet that is not openly indexed and made available via a web search. This includes any private information held on the cloud that is not listed on the Web.
VPN over Tor requires you to place trust in your ISP but not your VPN and is best if you want to avoid bad Tor exit nodes. Some consider VPN over Tor more secure because it maintains anonymity throughout the entire process (assuming you pay for your VPN anonymously). Although the official Tor Project advises against VPN over Tor, both methods are superior to not using a VPN at all. Tor over VPN also doesn’t protect users from malicious Tor exit nodes.
Can You Access The Dark Web With A VPN?

So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions.
Scammers prowl the dark net, launching fake storefronts that vanish overnight, often with their victims’ money. In 2017, a global police operation brought down AlphaBay, the dark web’s largest illegal marketplace, shaking the underground economy. The node requests the data from this server and forwards it to the user.
PIA is popular in the USA because it offers servers in all 51 states. People in the United States and abroad can use it to venture into the dark web in privacy. With RAM-based servers in 90+ countries and features like WireGuard, IPv6 leak protection, and a kill switch, worries are over. For example, legitimate sites, such as the BBC, the New York Times, ProPublica, and Facebook, have made their sites accessible as a Tor Onion URL to help people avoid government censorship. While the Tor network was not created for illegal activities, as it’s harder to trace websites to their physical location, cybercriminals have also adopted it to host their websites.