Flare, for example, enables you to automatically scan the clear & dark web for any leaked or stolen account credentials. By doing this, you can find your credentials for sale on the dark web and secure them before they are exploited. Stolen credit cards are also harmful to the businesses from which they were stolen in the first place. Customers whose payment information was stolen are less likely to want to continue doing business with your organization after a hack and your organization may sustain long-lasting reputational damage. Many tracker apps link directly to bank accounts for up-to-the-minute info.

Breakdown Of The Threads Features Being Leveraged By Cybercriminals
Starting on September 12, 2024, SpyCloud security researchers noticed new accounts – some with upwards of over 12,000 followers – posting credit card details and even photos of physical credit cards and debit cards. Carders tend to target specific sites that don’t have VBV or other protections against fraud. For fledgling criminals who don’t know how to use stolen credit cards, there are plenty of free and paid tutorials for carding on the dark web.
Our investigation into the activities of b1ack’s Stash has unveiled a substantial threat to the security of payment card data across local banks. Analysis of the leaked data, likely sourced from phishing campaigns, suggests a high probability of the validity of these stolen cards based on the available information. A significant portion of this data was uniquely identified in our intel collection. This article explains how attackers obtain financial data, what happens to stolen data, and how do criminals sell stolen credit card details on the dark web.
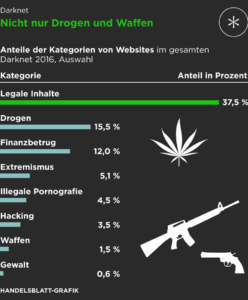
- Darknet markets — also known as cryptomarkets — provide a largely anonymous platform for trading in a range of illicit goods and services.
- Even if this “free sample” of credit card and debit card numbers is mostly just an attempt to gain attention in the cybercrime underground, the leak contains data that could still be useful for scammers, researchers say.
- It is understood that the data included such highly sensitive information as the primary account number of the credit cards concerned, along with expiration dates and the card verification value, CVV2, security code.
- Credit card theft has become one of the most common types of fraud, with the U.S. projected to lose a staggering $165 billion in the coming 10 years due to card abuse.
- They then extracted sensitive information, including credit card numbers, expiration dates, and security codes.
- Cybercriminals focus more on pilfering financial data like credit and debit card details, bank account numbers, and login credentials.
What To Do If Your Credit Card Information Is Stolen
Marijus Briedis, CTO at NordVPN, said the details for sale on the dark web are increasingly acquired through brute-forcing. Cass-Gottlieb told a parliamentary committee there had only been a few instances of fraudsters successfully scamming victims out of money by pretending to be from Optus. If the investigation reveals serious or repeated privacy breaches, the commissioner has the power to seek civil penalties through the Federal Court of up to $2.2 million per contravention. The cards affected are mostly VISA, Mastercard and American Express cards. However, we have also noticed that some search terms related to these topics appear to be shadow-banned by Telegram.
Using Tracker Apps To Monitor Your Card Data
The fraudulent credit cards were used to purchase gift cards, flights, hotels stays, and other goods and services. “The dumps also include magnetic stripe data, allowing criminals to create physical card clones,” Draghetti warned. It is understood that the data included such highly sensitive information as the primary account number of the credit cards concerned, along with expiration dates and the card verification value, CVV2, security code.
In contrast, breaches of CNP data rose from 18 percent to 25 percent in that same time period. Get Privacy’s iOS or Android app on your phone and receive alerts and notifications of account activity to stay on top of any suspicious transactions. We will also share some effective safety tips and discuss how virtual cards can help protect you from card fraud. Learn the basics of credit card cards, including features, fees, and rewards to make informed decisions about your credit card usage. Adding fullz to a card purchase increases the price by about $30 for a physical card and under a dollar for digital card info. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.
Social Security numbers and other national ID numbers are for sale on the dark web but aren’t particularly useful to cybercriminals on their own. That merchant specifically mentioned that using a stolen card on a store that uses Verified by Visa (VBV) will likely void the card. Verified by Visa is a service that prompts the cardholder for a one-time password whenever their card is used at participating stores.
India Data Breach: 460,000 Credit Card Details Put Up For Sale On Dark Web
These stats highlight the scale of credit card fraud on dark web markets. Since it was established in 2020, Real and Rare has been considered to be a stable credit card site that suffered very few downtimes. The number of card packages offered on the site has consistently increased, and today it also has an active Telegram channel from which it operates and sells stolen credit card details and announces new dumps. After it relaunched in June 2022, BidenCash initiated a promotional campaign that included sharing a dump of 8 million lines of compromised data for sale, which included thousands of stolen credit cards. In line with b1ack’s freebie marketing strategy, they announced the release of 1 million stolen payment cards for free on several popular carding forums on the last day of April this year.
The banks, lenders, and credit card companies are not responsible for any content posted on this site and do not endorse or guarantee any reviews. Credit card theft is typically proven through evidence of unauthorized transactions, often identified by the cardholder or through the bank’s fraud detection systems. Public Wi-Fi networks are usually not encrypted, which allows hackers to easily intercept your data. This kind of network is typical for hackers to monitor your activity and capture your credit card number during transactions. Of the Italian cards, roughly 50% have already been blocked due to the issuing banks having detected fraudulent activity, which means that the actually usable entries in the leaked collection may be as low as 10%.
Threatpost

Several new cybersecurity scams and malicious activities originate from these underground forums. Threat actors discuss and share knowledge on new hacking techniques and tools. Some senior threat groups even provide tutorials and share their attacking procedures to the budding hackers. Threads is a feature-rich platform, and threat actors are clearly using Threads’ features and functionality, including taking advantage of suggested content, polls, and trending social tags to promote stolen financial data.
Using Virtual Payment Cards

And payment processors can block all transactions if carding attacks are not handled quickly, which can result in lost revenue to the retailer. Financial data can leak in many ways—through phishing attacks, data breaches at online services, or poor account security. Even in regions like the EU, where banks are legally required to implement strong customer authentication, criminals continue to find ways to bypass these safeguards.
Dark web transactions play a key role in fund transfers for credit card fraud. Cybercriminals use cryptocurrency to buy and sell stolen card data anonymously. With the growing threat from cybercriminals who sell stolen credit card information on the deep web and dark web, businesses need to stay ahead of the game. Over the years several advanced tools have been developed to help track and prevent such fraudulent activities. In addition to these types of listings, there are other free tools usually available on credit card sites. These tools include for example different types of checkers, which assist threat actors in verifying whether the stolen card information they possess is valid and can be used to make unauthorized purchases.
Get Threat Assessment Report
Full or partial credit card details are commonly sold on the dark web, including BIN numbers, credit card numbers, expiration dates, and CVV numbers. The data posted on these online illicit shops is a goldmine for threat actors who are looking to commit financial crimes. It provides them with valuable information needed to carry out a variety of attacks. Wizardshop.cc was established in 2022, and offers a wide range of leaked CVVs, database dumps and even RDPs.

Exploring Benefits And Risks Of Using Credit Cards Or Card
A staggering 1.2 million credit cards were leaked on the dark web, making it a massive data breach. Most of use just have the standard personal account, but Premier and Business accounts also exist, and are up for sale on the dark web. But those tiers don’t have much influence on dark web prices, which are largely governed by account balance. Unlike carding shops, which primarily focus on the trade of information, carding forums serve a broader purpose within the cybercriminal community.
Don’t wait for the company to take action – take control of your own safety by being vigilant and reporting any suspicious activity. Monitoring your financial accounts for signs of fraud is crucial, so keep a close eye on them. Join the Breach and Attack Simulation Summit and experience the future of security validation. Hear from top experts and see how AI-powered BAS is transforming breach and attack simulation.
BidenCash shop was established in April 2022, following the seizure of other card shops and carding platforms by the Russian authorities. Since its inception, it has been attracting the attention of both old and new cybercriminal customers. With the increase in the size of the target, cybercriminals are stepping up their game. Security researchers are discovering more sophisticated bots that are capable of closely mirroring human behavior, making them very difficult for traditional security technologies to detect. A carding attack not only impacts the person whose card has been compromised.
In 2006, TJX Companies, the parent company of retailers like TJMaxx and Marshall’s, was a target of a massive cyber-attack that stole 94 million credit card numbers. In 2019, hackers infiltrated a major credit card processing company, compromising over 1 million credit card numbers. Even in a digital age, criminals still steal mail for financial documents containing sensitive information. Comparitech researchers sifted through several illicit marketplaces on the dark web to find out how much our private information is worth.
The risk exposed consumer data poses for your business can impact your organization’s bottom line just as much as if the threat were to come from inside the house via an exposed employee or vendor. It’s imperative you have visibility into the stolen data being used to potentially create fraudulent accounts or transactions. In some cases, we observed sample “fullz” posted on Threads with a critical piece of information (such as the CVV) omitted to drive interested parties to a website, Telegram channel, or direct messages on another platform. There are also scammers that advertise using stolen cards recycled from other sources, entice people to buy a fake premium offering, take their money, and then never deliver any additional data. Even if this “free sample” of credit card and debit card numbers is mostly just an attempt to gain attention in the cybercrime underground, the leak contains data that could still be useful for scammers, researchers say. Once your personal information hits the dark web, it’s nearly impossible to remove it.