
You can check out this guide on the best antivirus software applications today. If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed.
Illicit drug sales, for example, are promoted on social media, where platform features such as recommendation systems are affording new means of illicit drug supply. Monopoly Market is a newer darknet market that has quickly gained popularity due to its focus on security and privacy. It only accepts Bitcoin as a form of payment, but it uses a unique payment system that helps to protect the anonymity of its users. Monopoly Market also has a strict policy against listing certain types of goods and services, such as weapons and child pornography. White House Market is a newer darknet market that has quickly gained popularity due to its focus on security and privacy.
Understanding these emerging threats is essential for anyone navigating the digital landscape, from cybersecurity professionals to everyday users. Staying informed and proactive is crucial in combating the ongoing challenges posed by the darknet and ensuring a safer online environment. As regulatory scrutiny increases on mainstream cryptocurrencies, criminals will adapt and find ways to utilize less traceable options. As we move into 2025, the ever-shifting landscape of cybercrime continues to evolve, with the darknet remaining a significant hub for illicit activities. From emerging technologies to shifting criminal tactics, understanding these trends is critical for cybersecurity professionals, law enforcement agencies, and the general public alike.
Reddit Subreddits For Darknet Markets
- Additionally, deploying endpoint protection solutions safeguards devices from malware and other malicious activities.
- While the darknet is present globally, Australia has been a key player in the darknet industry.
- The maximum length of usernames is sometimes set at 16 or 20 characters, but half of the markets in our study had no length limit (i.e. we achieved successful registration with more than 64 characters).
- So, that means that the number of pages increased by over 100 trillion in just over three years.
- While our results may not be exhaustive, we believe the security mechanisms implemented by the market interact somehow with potential market closures.
For instance, our focus extends beyond security mechanisms specifically designed to prevent phishing attacks (though some are indeed effective against such attacks). We also cover mechanisms related to DDoS attacks, account, web and financial security, together with some other related topics. The trends observed in dark web markets are very dynamic and ever-changing.
National Cyber Authorities Launch OT Security Guidance
Ads must be relevant to r/darknet, as well as posted in the correct sticky. Posts which violate this rule will be removed; repeat offenders will be banned. This includes discussion of buying, selling, trading, methods, dumps and vendors for anything Cash App to Credit Card. It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links.
What Is Tails Software Used For?
French, Dutch, and select EU passports all cost $3,000 apiece, Polish passports went for $2,500 each, US passports sold for $2,000, while Lithuanian passports cost $1,800 each. Other popular physical documents included EU driver’s licenses ($2,000 apiece), EU national IDs ($1,700 on average), forged US green cards ($450), and IDs of several US states ($200). A recent study found that only a tiny portion of Tor’s daily users connect to the Dark Web with the intent to engage in illicit activities. According to estimates, the size of this hidden web stands at 7,500 terabytes — making it about 400 times larger than the Surface Web.
Only 67% Of Tor’s Daily Users Engage In Illegal Activity On The Dark Web
As rapidly developing business, dark web markets are undergoing changes all the time. The current literature on them has covered well various important features, providing valuable insights for the understanding of how dark web markets operate. For instance, Christin 9 collected and analysed data for eight months (between late 2011 and 2012) for a longitudinal study in the most notorious dark web market at the time—Silk Road. Van Wegberg et al. 32 analysed no less than six years of longitudinal data from eight dark web markets. Both works find out that the business models of these markets is maturing.

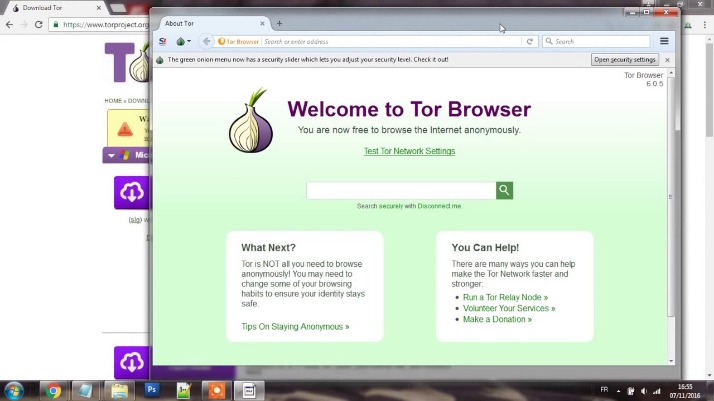
The most popular darknet in Australia and worldwide is TOR, thanks to its complex network of relays spread globally. Rerouting your traffic adds more layers of encryption to your data, which hides your true IP address better. Darknets are online overlay networks one can use to access specific websites and web pages. They use specific software, authorization, communication protocols, and configurations to provide access to these sites.
Two-Thirds Of Organizations Have Unfilled Cybersecurity Positions
Launched after the takedown of AlphaBay in 2021, Abacus Market has rapidly risen to prominence. It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data. The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. Market lists, often updated regularly, provide users with direct access to active onion URLs, reducing the risk of phishing or scams.

Report It To The Authorities (if It’s Safe To Do So)
As the Internet of Things (IoT) continues to expand, so do the opportunities for cybercriminals. The increasing number of connected devices creates a larger attack surface, and many IoT devices are inadequately secured. According to a report by the International Telecommunication Union (ITU), IoT vulnerabilities are expected to triple by 2025. Think of the Dark Web as what you find while driving on the darknet highway—the actual sites and services.
Further Reports
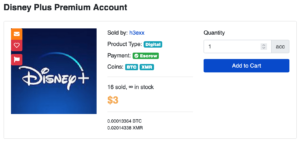
A Distributed Denial of Service (DDoS) attack is designed to disrupt access to websites and other internet resources. This is achieved by overwhelming the targeted website’s server with thousands of connection requests, causing it to crash. They also offer access to online subscription services for cheaper prices—but customers have to gamble with the chance of being caught. Prices of hacked cryptocurrency accounts still remain overall the highest among all hacked online accounts. This indicates that hacking such accounts still remains extremely profitable.

These included an advanced encryption program known as “Pretty Good Privacy” and a cryptocurrency called Monero. Unlike Bitcoin, which records every payment on a public ledger, Monero conceals all transaction details by default which makes them nearly impossible to trace. Ransomware attacks have surged in recent years, and the RaaS model is becoming increasingly popular on the darknet. This model allows even low-skilled cybercriminals to launch ransomware attacks by purchasing or renting malware from experienced developers. A report from the Cybersecurity and Infrastructure Security Agency (CISA) indicates that ransomware attacks have increased by 150% since 2020. The surface you see with search engines like Google is the “clearnet,” but a much larger portion lurks beneath the water – the deep web.
- Cybernod provides cutting-edge security solutions, helping businesses detect exposed credentials, security vulnerabilities, and cyber threats before they escalate.
- The Moneyzine.com stats team will then look at the usage data for Tor, the go-to browser for accessing the Dark Web.
- It was touted as a major policing win and was accompanied by a slick cyberpunk-themed video.
- These are the most expensive items on the Dark Web markets by a long shot.
- Small businesses have increasingly become prime targets for cybercriminals operating on the dark web.
What Are Initial Access Brokers (IABs)?
The best darknet markets in 2025 prioritize security, reliability, and user experience, making them ideal platforms for the drug trade. These markets leverage advanced encryption technologies, such as Tor and PGP, to ensure that transactions remain private and secure. Vendors and buyers benefit from end-to-end encryption, which protects communication and payment details from unauthorized access.
Grams Darknet Market
In 2023 the dark web has over 2.5 million daily visitors, and it’s estimated that more than half of those visitors have participated in illegal activities. What’s even more alarming is that in April 2023, daily dark web visitors rose by 200,000 to reach 2.7 million. IABs are cybercriminals who sell access to compromised networks — often through the dark web — to ransomware groups or other malicious actors.
Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed.
We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. You should never use your personal information on the dark web anywhere else in your life. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing.



