This structure allows the program to detect subtle patterns in data, improve its accuracy, and adapt to...
Uncategorized
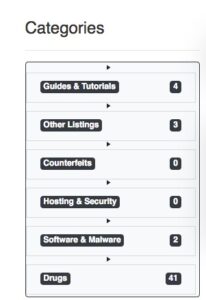
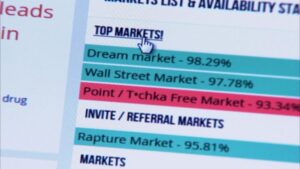
Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark...
Cypher darknet market is not just a transaction for us – it’s an opportunity to build lasting...
Based on in the CYPHER Stent PostMarket Registry in 2003 and the e-SELECT post-market. Cypher CYP ICO...
Cypher beckons those in pursuit of a novel and evolving adventure into the deeper echelons of the...
Everything in the interview is extraordinary, tor market as Blue Sunset has many clients and he remembers...
If you come across any instances of credit card fraud or encounter suspicious activities, it is essential...
For the first time, FBI agents from all of the bureau’s field offices visited buyers to tell...
Currency use shows a privacy-minded crowd—BTC takes 60% of trades for its speed, while XMR’s untraceable edge...
This way, Tor makes it much more difficult to trace the traffic back to the original user....