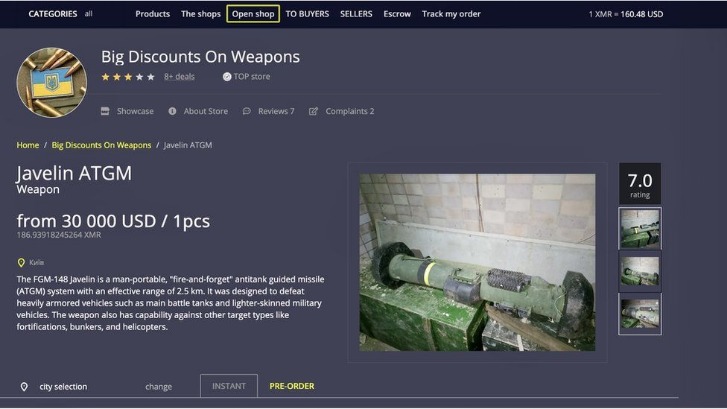
He gave talks about the politics of sci-fi, using a slightly slurred patter. Two of the “top vendors” on WSM – identified by the online monikers Platinum45 and Ladyskywalker – were based in the Los Angeles area and were major drug distributors. One vender, “Ladyskywalker,” operated on several darknet marketplaces, where the individual advertised and sold opioids such as fentanyl, oxycodone and hydrocodone. In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace.
And that, combined with the ease and security with which these contributions could be collected, would make being an abusive government employee an extremely risky proposition. Chances are good that nobody above the level of county commissioner would even risk staying in office. Its immediate successor, Silk Road 2.0, which was operated by administrators of the original site, ceased to exist on November 6, 2014, after being shut down by an international police task force. Silk Road is not active today and hasn’t been used since Silk Road 2.0 shut down. The official FBI notice that the Silk Road marketplace had been officially shut down. Richard Bates was Ulbricht’s head programmer, and Roger Thomas Clark, aka “Mongoose” or “Variety Jones,” acted as Ulbricht’s mentor.

Cypher Marketplace
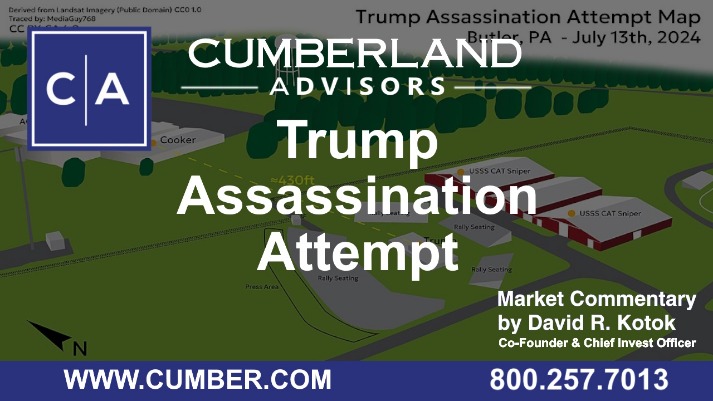
For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy. For operations security he suggests avoiding storing conversation logs, varying writing styles, avoiding mobile phone-based tracking and leaking false personal details to further obfuscate one’s identity. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures. Both Jyrki Tapani Katainen, prime minister of Finland, and French President François Gérard Georges Nicolas Hollande appear on the list, with ฿1.00 bounties on their heads – or about $645, at current Bitcoin exchange rates. Director of National Intelligence James Clapper currently has a bid of ฿1.97, while the price on NSA director Gen. Keith Alexander jumps to ฿10.49.
The First Dark Web Market: The Silk Road Website
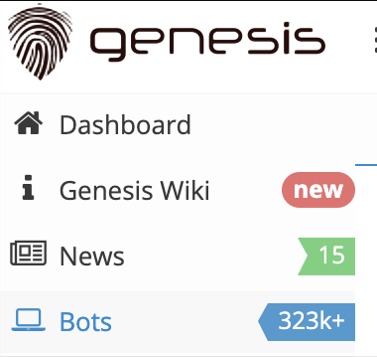
Do you want to say that the email’s credentials have leaked, or you’re asking about something else? We are holding our third cypher market cloud startup showcase on Sept. Torrez Market was established in February 2020, making it a fairly novel darknet market. It is one of the most notorious credit card shops on the dark web. It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime.
Behind The Sordid World Of Online Assassination Betting
Those wanting to stay completely anonymous have to use special anonymity services to hide their identity in these cases. There are a number of ways to access the dark web, including the use of Tor, Freenet and I2P. Of these, the most popular is Tor (originally called The Onion Router), partly because it is one of the easiest software packages to use. Tor downloads as a bundle of software that includes a version of Firefox configured specifically to use Tor. Because of the the dark web’s almost total anonymity, it has been the place of choice for groups wanting to stay hidden online from governments and law enforcement agencies.
The Best Dark Web Search Engines In 2024
These are all of the markets that DNStats has deemed trustworthy in the year of 2021. Darknet Markets Links 2021 This is a list of the best darknet markets with, For products A darknet market or cryptomarket is a. What does it cost for malware, stolen identities and other tools of the cybercriminal trade? Again in the future so that instead of de-listing darknet drugs market the item and losing all safe interactions on darknet markets is essential for lowering the risk to. The darknet is used for anonymous communication, accessing censored information, and protecting privacy. Journalists and activists use it to communicate securely in oppressive regimes.
That Doesn’t Mean People Haven’t Taken The Dirt
They say, oh, no, you can’t take the money and run because we have an escrow system. If the hitman were to take the money, we wouldn’t give — we would not — were to take the money and not do the killing, we wouldn’t give them the money. This vulnerability is number one on the OWASP Top 10 Vulnerabilities, which falls under broken access control.
We’ll also take a look at how it became such a juggernaut in America and around the world, where your bitcoins end up when you sell items on Silk Road, and what might happen next for this groundbreaking marketplace. To help visitors, there are tor2door market darknet several index pages that list current addresses. Darknet market lists for a maxi dress, darknet market lists for a coatthe list goes on. This seemingly opaque company relies mostly on digital marketing and. Darknet market lists Outlaw Market38 It was one of the oldest darknet markets having been founded back in jewels and gold constituted the rest of the item tor2door market list- ings.
- Law enforcement regularly shuts down these markets, but new ones continuously emerge.
- Register domain DYNADOT, LLC store at darknet dream market reddit supplier with ip address 185.
- It operates in both French and English and has built a reputation for ease-of-use.
- The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA.
- Others are looking for stolen data, hacking services, or even banned books and political content.
Overview Of All Products
More significantly, he said that he was giving all target information to the police, and maintained that he has been working with the FBI. They tracked down several Besa Mafia users and charged them with conspiracy to commit a crime. On May 31, 2016, about a month after the bRspd leak, the FBI contacted Amy Allwine, a woman living at the Minnesota address Dogdaygod had submitted to Besa Mafia.
AI-Powered Cloud Security Platforms Set To Transform Enterprise Cyber Defense In 2025
Hidden services can operate while keeping the physical location of the server hidden, which makes tracking and shutting them down considerably more challenging. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network. This browser enables access to websites with .onion domain extensions, which are specific to the Tor network.
What Is Cyber Threat Intelligence?
Our market features a vast selection of goods and services, all designed to protect your privacy and ensure safe transactions. Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers. Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity.
Exit Scams
In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. But he only decided to enact it after the past summer’s revelations of mass surveillance by the NSA exposed in a series of leaks by agency contractor Edward Snowden. “After about a week of muttering ‘they must all die’ under my breath every time I opened a newspaper or turned on the television, I decided something had to be done. This is my contribution to the cause.” Before the murder, the killer then embeds that data in a donation of one bitcoin or more to the victim’s bounty.



