
As long as you are vigilant about your online activity, there aren’t any issues. The maximum trouble you can get into on the dark web is visiting political forums or marketplaces. In that case, the government might flag and monitor you even if you’re not a participant or trader. The safer option of the security settings only disables the JavaScript on websites that aren’t “https” protected, while the safest option disables JavaScript on all websites. In this case, you connect the VPN service and then launch Tor Browser.
Step 3: Launch Hyphanet
That means that Google wants to minimize the amount of time users spend searching for certain queries. Did you know that Google only shows you a glimpse of all the websites that actually exist? The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search.
- As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing.
- Ruheni explains complicated technical concepts clearly and simply.
- A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous.
- While the Tor network was not created for illegal activities, as it’s harder to trace websites to their physical location, cybercriminals have also adopted it to host their websites.
Choose A VPN
Its deep insights into cybercrime forums, compromised card databases, and exposed assets give security teams a critical edge. Choosing a dark web monitoring tool requires a lot of factors, including price, availability, and many other things. However, effectiveness comes down to how well the tool aligns with your risk profile and operational needs. Malware, ransomware, and hacking tools are also readily available for purchase or rent, enabling attackers to launch sophisticated campaigns. Additionally, forums facilitate the exchange of exploit kits and zero-day vulnerabilities, which can be weaponized before patches are released. The anonymity of the dark web makes it a fertile ground for coordinating cyberattacks and sharing illicit services without detection.
Best Practices For Accessing The Dark Web
Dark web sites are hidden by non-indexing, making them completely anonymous. You’ll need a purpose-built browser that uses The Onion Router (TOR) to access dark web content. Because of their anonymity, dark web sites are breeding grounds for illegal activity and transactions.
Choose An Overlay Network
No node can track the complete path the traffic has taken, and more importantly, neither can anyone who finds it on the other side. Only the entry node can view your IP address (more on how to stop this happening later). To access the Dark Web, you have to use a browser called Tor, also known as The Onion Router. This is the only way to ensure a maximally anonymous – as well as safe – browsing experience on the Dark Web. With dangers like this in mind, it’s even more important to stay safe when surfing the Dark Web than any other part of the internet.
Step 5: Exit Safely
Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. It is a relatively new provider but offers better features than most established VPNs. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. Also, use an effective antivirus program to check threats if you decide to download files. You can check out this guide on the best antivirus software applications today.

In addition, even if the Tor node fails, your data won’t be exposed because the VPN’s encryption still holds up. As mentioned, we recommend using a safe provider like NordVPN, which also offers Onion Over VPN servers perfect for accessing the dark web safely. The term ‘deep web’ doesn’t mean anything nefarious – it’s estimated to make up about 99% of the entire web. It refers to the unindexed web databases and other content that search engines can’t crawl through and catalog. The deep web is like an archive, containing an unsorted pile of websites and resources that are largely inaccessible to normal users.
Regularly Update Your Software
It aims to preserve the internet’s scientific and cultural heritage. Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy. ProtonMail is a Swiss-based email service that is very easy to use. You are not required to provide your personal information to create an account.
Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network. Hacker services against banks and other financial institutions are offered there. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes. The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures.
Recognize And Avoid Phishing Links

While there are other dark web browsers, they’re generally unreliable, unsafe, and complicated. The safest way to access the dark web on your phone is by using the official Tor Browser for Android or the Onion Browser for iPhone. That said, illegal actions remain illegal, whether on the dark web or not. Some regions ban the Tor network entirely, such as China, Russia, and Iran, so check your country’s laws before using it.
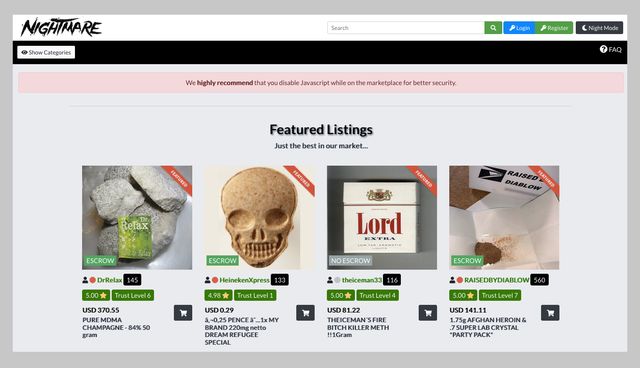

But you can face criminal charges if you use the dark web to sell or purchase illegal firearms, drugs, pornography, stolen passwords, hacked credit card account numbers, or other items. For example, dissidents who fear political prosecution from their governments might use the dark web to communicate with each other. As many as 70.79% of users claim to use the Tor browser for anonymity, 62.28% said they use it for additional security, and 27.07% used it out of curiosity about the dark web. The dark web was created not long after the first message was sent in 1969 over the original internet, ARPANET. Covert networks — or darknets — emerged quickly and provided users with private networks to communicate. If your details have been exposed in a data breach it’s possible that they’re on the dark web.
Deep Net Websites
Due to its anonymity, carding, fraud, and counterfeiting businesses are thriving on the dark web. Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information. The Dark Web has a social media platform called the Dark Web Social Network (DWSN), which is similar to regular social networking sites.



