
No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet. Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web.
Step 2: Download And Verify The Tails OS Image

Other privacy networks like I2P, Lokinet, and Freenet offer different layers of security and anonymity. Each tool works differently, and some are better suited for specific use cases than others. Your information might be on the dark web if it was exposed in a data breach, sold, or stolen by hackers. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data.
What Should I Do If My Social Security Number Is On The Dark Web?
As always, protect yourself from online threats with mobile Android security or iOS security software. And use a VPN for Android or a VPN for iOSto get a secure, private connection. Before accessing the dark web, install strong security software to help keep your device protected.

Step 7: Use Additional Security Tools
This creates a privacy risk even if they can’t see what you’re doing on the dark web. Plus, in some regions, accessing the dark web alone may raise suspicion or get you flagged for extra monitoring. To access the dark web safely, it’s necessary to use a dark web browser like Tor in combination with trusted dark web directories and search engines to help you find reliable sites. You should also make sure your device is protected by strong antivirus software, and consider using a VPN to mask your activity on the dark web. The Tor Browser is the safest and most trusted way to access the dark web. That said, there are still some ways to protect yourself when using the Tor Browser.
Is The Dark Web Truly Safe?
Most dark web sites are unregulated, which means that there are fewer mechanisms in place to prevent you from accidentally downloading malware. It’s a good idea to connect to a trusted VPN before you even open the Tor Browser to access the dark web. You can download the VPN app from the provider’s official website or your device’s app store. Run the setup file and then simply follow the on-screen instructions.
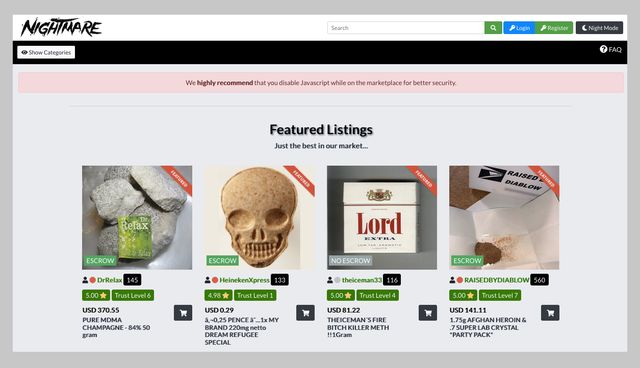
Commercial Services
Don’t download anything unless you’re absolutely sure it’s safe. Don’t log into any real accounts, reuse usernames, or enter any personal details. Treat every site as untrusted unless you’ve verified it from multiple sources. This hides your Tor usage from local networks, masks direct Tor connections, protects against network-level surveillance, and reduces the risk of being flagged for accessing privacy tools.

Dark Web Search Engine
If you want to mitigate that possibility, downloading a VPN is the best way to do so – it funnels your traffic through a private server and keeps your IP address hidden. There are plenty of services that offer a VPN over onion feature, which will keep you secure and private online. If you’ve already done that, or even something similar, that’s good news – you’re already a deep web user accessing information not available through common search engines. Everything from social media data to medical records are held on the deep web, as is all your email information. In addition, even if the Tor node fails, your data won’t be exposed because the VPN’s encryption still holds up. As mentioned, we recommend using a safe provider like NordVPN, which also offers Onion Over VPN servers perfect for accessing the dark web safely.
Research of the dark web is legal as long as national or international laws are not broken. Never install extensions or additional add-ons, even if they seem useful. They change your browser fingerprint and make you easier to track. Underneath it are deeper layers that aren’t visible through normal browsing. Install Avast SecureLine VPN for iOS to protect your privacy and keep your data from falling into the wrong hands.
Secure Your System And Mental Well-being
Though it still requires being routed through Tor (it is not a deep web browser by itself), it provides a clean, quick, and privacy-respecting base to use for your anonymous browsing sessions. Fun fact is that Tor Browser (Tor network is a different thing than the browser) is built from Firefox ESR (Extended Support Release), a modified version of Firefox. So, it’s worth using Firefox if you’re up for the tweaks needed. Tor Browser has an official Android app if you want to use it on mobile. For iOS users, while there’s no official Tor app for iOS, a couple of options, including Orbot and Onion Browser, recommended by the Tor Project itself, exist. Just below the surface is the gigantic “deep web.” Here, you’ll find all things that require a login, like your email, bank account, corporate intranet, government databases, etc.
- For built-in Tor over VPN functionality, NordVPN operates specialized servers that automatically route you through the Tor network.
- Your clear web browser activity can be logged and tracked by advertisers, governments, and your ISP if you’re not using a VPN.
- By disabling, you reduce such attacks’ potential (especially on untrusted websites).
- In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous.
Malware And Viruses
We understand that because of the reputation looming over the dark web as being so dangerous, mysterious, and whatnot. Some sites are safe to use, especially those where you don’t need to provide sensitive information to use. Private Internet Access even offers the Shadowsocks proxy for added security. There’s also MultiHop that boosts your encryption, along with MACE which blocks tracking. PIA doesn’t pull punches, so it strikes back against its competition with a proven-in-court no-logs policy, split tunneling, and even port forwarding to diversify its apps.
How To Minimize Risks:
If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. VPNs are also used for accessing geo-locked content hosted by streaming services. The best VPN options are paid-for and subscription-based, as many free options will either throttle your speed or collect your data. As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet. This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources.
Everything else on the internet is located on either the deep web or the dark web – and they aren’t as easily accessible, or as safe. So if you’re planning on accessing the dark web, here’s all you need to know to access it safely. Venturing into the dark web with your phone is a journey into a lesser-known internet space.



