
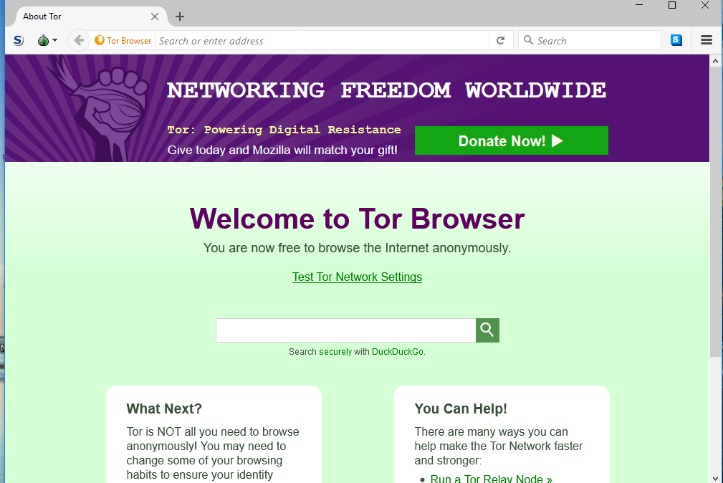
Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators. But let’s be realistic, the best defence isn’t just playing detective after the fact. It’s making sure your sensitive information never lands there in the first place. You have successfully accessed DuckDuckGo on the Tor Browser, enabling you to search the depths of the dark web while preserving your privacy and anonymity. The next step will guide you on how to navigate the dark web using DuckDuckGo effectively.
If you want to use Tor privately, you can use either a VPN or Tor Bridges (Tor nodes that are not publicly indexed). Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. Journalists and whistleblowers, including Edward Snowden himself, often use the dark web and Tor to exchange sensitive information. For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. Discovered pages are indexed in an extensive database and ranked based on numerous factors. When you search a term (or query) in a web browser, the search engine combs through the database to find relevant results and serves them up on SERPs.
If used responsibly, it serves as a valuable tool for privacy, free speech, and secure communication. However, engaging in criminal activities on the dark web can lead to serious legal consequences. While Bitcoin and other cryptocurrencies provide some level of anonymity, blockchain analysis tools can trace illicit transactions. People in countries with restricted internet access use the dark web to bypass government censorship and obtain unbiased news.
- Another great source to find and explore dark web marketplaces or other sections is to visit Reddit’s resourceful forum.
- Learn more about what the dark web looks like, then get a VPN to stay more private when you browse the web.
- According to Recorded Future research1, out of 55,000 onion domains discovered, only 8,400 have a live site.
- There are reports of illegal services on the dark web, ranging from paid assassinations to the trafficking of sex and weapons.
- A phishing website or link is one that appears legitimate but is actually a trick designed to make you hand over your personal information to hackers and other bad actors.
Accessing The Dark Web On Various Devices
Your access to illegal content, even if it is unintentional, can violate laws in many countries. The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network. There are many different ways to access the dark web, but navigating it can be tricky and dangerous if you don’t know what you’re doing. A VPN will give you an extra layer of protection and anonymity, making it much safer to explore the dark web. Then there’s the less popular VPN over Tor, which is advised against by the official Tor Project.
- Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors.
- It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee.
- Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin.
- When both buyers and sellers are anonymous, the credibility of any ratings system is dubious.
- Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing.
- Keep in mind that in some regions like China and Russia, it’s illegal to use anonymizers.
Dangers Of Accessing The Dark Web
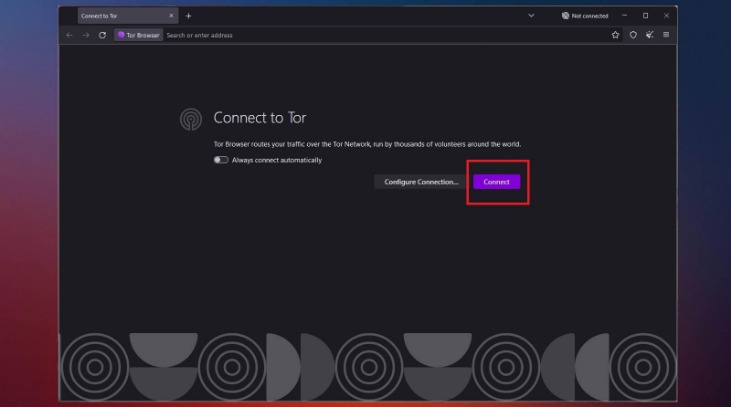
That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you. It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users. Obviously not all Tor users, but you never know whether someone might be looking into you. It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity. So, to get into the Tor network, follow the steps I’ve listed below.
Why Use Tor For Accessing The Dark Web?
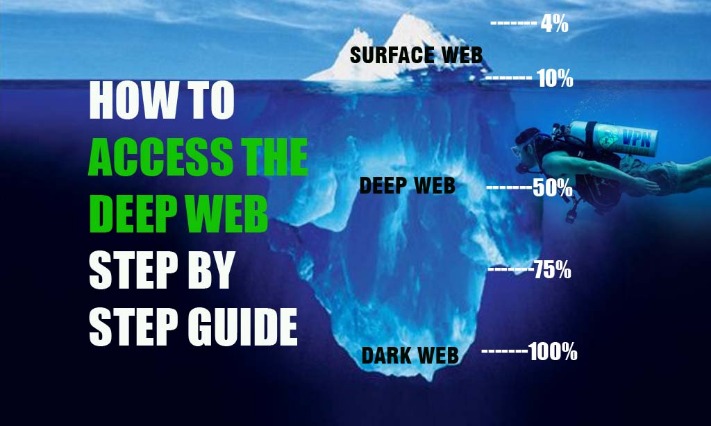
The dark web is a small portion of the deep web that has been intentionally hidden and is inaccessible through standard web browsers. To access it, you need dark web browsers like Tor, which allows users to browse anonymously by bouncing their connections through a global network of volunteer servers. Sure, you’ll find a fair share of illegal activities and dubious marketplaces, but the dark web is also home to a variety of content that isn’t inherently evil.
There are numerous phishing sites, too, as explained earlier, designed to fool users into giving up their personal data. Many cybersecurity and tech experts recommend using a VPN whenever you want to access the dark web via the Tor Browser or any other specialist browser. A quality VPN like ExpressVPN will encrypt your internet traffic and mask your IP address, providing an extra layer of anonymity when establishing the initial Tor connection. Given the many cyber threats present on the dark web, it’s recommended to be extra careful when you access it. Accessing it without proper protection exposes you to surveillance, tracking, and potential security risks. If you need to access the dark web, NymVPN can add an essential layer of privacy and anonymity, encrypting your connection before you even access the Tor network.
Is It Illegal To Visit And Use Dark Websites?
Dark web monitoring platforms provide secure communication channels for individuals seeking to expose information without fear of retribution. Additionally, the Dark Web serves as a haven for those in censored environments, offering access to restricted information and enabling the free expression of opinions. Unlike the surface web, which can be indexed by standard search engines, the dark web exists on encrypted networks and hosts websites with random, complex URLs. This layered encryption and anonymization make it difficult for authorities or outsiders to trace activities or identify participants.
Maintain Anonymity
This dual layer of security allows you to explore the dark web with confidence. Files from the dark web can easily contain malware or tracking code. If you must download something, scan it with antivirus software and consider using a separate device or virtual machine. You should also avoid clicking on suspicious ads or pop-ups, as they may contain malware or lead you to scam sites. Even if they aren’t actively malicious, they might still have weak security or expose you to threats. Additionally, make sure that you only download the Tor Browser from the official website.
Fraud and scams run rampant on the dark web, including offers too good to be true and fake services requiring upfront payment. Hackers sell access to email accounts, social media profiles, or other information that can be used for identity theft. If you use Tor to access the dark web or unblock websites, connect with a VPN for extra security. Because of the dark web’s association with illicit activity, your use of Tor may be tracked by your ISP, drawing unwanted scrutiny to your browsing behavior. The dark web limits online tracking, and there are many legitimate reasons people like journalists and activists use the dark web to remain private.
Common Dark Web Threats
The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below. No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet. Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top.
It would be problematic if someone could open your private email chains through a simple Google search. An easy way to think about this is if you need a username and password to access it, it’s a part of the deep web. These URLs are usually very long, consisting of a random jumble of letters and numbers. Though you likely won’t remember the addresses of onion websites, you can find these URLs on various websites on the internet. Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web.
What’s The Difference Between Tor And VPN?
Another vital precaution is to ensure that your .onion URLs are correct. Onion URLs generally contain a string of seemingly random letters and numbers. Once you are certain that you have the correct URL, save it in an encrypted note—the Tor browser will not cache it for later. Otherwise, there’s a good chance of falling victim to a phishing scam like this fake Bitcoin mixer. Reddit is also a valuable resource for finding the dark net or deep website you’re looking for.
The dark web refers to websites that are not on the regular internet but are instead hidden in a private network that is only accessible using specialized web browsers, such as the Tor Browser. If you want to access the dark web, your first step toward a more private experience should be to secure your internet connection and data with a reliable VPN. Staying safe on the unregulated dark web requires vigilance, and its seedy reputation, fostered by controversy like that surrounding Silk Road, is well-earned.
For example, your Geekflare.com—your trusted business resource for growth exists on the surface web. To reach Geekflare.com, you can either type its URL in your standard web browser or search for Geekflare in your favorite search engine. Setting up I2P requires more configuration on the user’s part than Tor. I2P must be downloaded and installed, after which configuration is done through the router console.
Always double-check URLs, and don’t download files unless you are sure of their source. This simple habit can prevent many potential security issues and help you avoid getting hacked. The dark web is like the mysterious basement of the internet — dimly lit, a little spooky and filled with stuff you probably shouldn’t touch. But don’t let its reputation fool you; the dark web isn’t all shadowy figures in hoodies plotting world domination.
A VPN encrypts your traffic before it reaches the Tor network, preventing your ISP from seeing that you’re using Tor. To understand how this is possible, we need to see how the web has many layers, and not all content is publicly available from a search engine query. In this guide, we’ll explain what the dark web is, how to access it safely, and why using a VPN (Virtual Private Network) with Tor is essential for anonymity.



