
The dark web is a part of the internet consisting of hidden sites that aren’t indexed by conventional search engines. While the Tor Browser is designed to protect your privacy, it’s not 100% safe on its own. Without a VPN, your ISP can see that you’re using Tor, and the first Tor server (entry node) can see your real IP address. Additionally, if Tor leaks, your IP address will be exposed to everyone.
What’s The Difference Between Tor And VPN?

For more information, read more about the most secure email service providers in my other post. Now that you’ve completed the download, it’s time to install the Tor browser on your device. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network. The dark web is a decentralized web, which means that the data is stored on many different servers around the world. It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims.
- The dark web is notorious for hosting a wide range of cyber threats that pose significant risks to individuals and organizations.
- The history of the Dark Web is intricately tied to the development of internet technology and the ongoing pursuit of online anonymity.
- Moreover, hackers who offer their services over the dark web have also targeted financial institutions and banks.
- It is a good way to prevent third parties from tracking online activities.
- In certain countries, the dark web facilitates political discourse and conversation that would otherwise be censored, outlawed, or eradicated in entirety.
- Many journalists, whistleblowers, activists, and even government agencies use it for privacy and secure communication.
Are Onion Sites Safe To Visit?
The most common tool for accessing the Dark Web is Tor (The Onion Router). Tor provides anonymity through a process known as “onion routing,” where internet traffic is encrypted and passed through multiple network nodes. Each node decrypts just enough data to know the next destination but not the origin, making tracing the connection back to the user exceptionally difficult.
While many dark marketplaces have been shut down by authorities, new ones soon appear in their place. The threats of online browsing can extend into the unplugged world if your computer or network connection can be exploited. Anonymity is powerful with Tor and the framework of the dark web, but it is not infallible.
Hacking And Cybercrime Services
The browser generally updates automatically, but it’s smart to check periodically for manual updates. VPNs also guard against DNS and WebRTC leaks, which can expose your real IP. Be sure to configure both your VPN and browser to block these leaks. Popular VPNs like ExpressVPN and NordVPN come with built-in leak protection. Additionally, check the Block pop-up windows and Warn when websites try to install add-ons settings.
The Tor Browser is the most trusted option for accessing the dark web, but it’s not invincible. In fact, the network has faced real challenges, including seven months of DDOS attacks in 2022 (Securityaffairs)2. In this article, I’ll guide you through the safest way to enter the dark web, like downloading Tor securely, booting from Tails, and using a trustworthy no-logs VPN. By the end, you’ll know how to explore with confidence while keeping your data safe.
How To Change The Tor Browser’s Security Settings On Android
The easiest way to access Tor is through a special browser known as the Tor Browser. You might want to hide your Tor Browser download using a VPN and your existing browser’s private/incognito mode. Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences. When both buyers and sellers are anonymous, the credibility of any ratings system is dubious. Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers.
Despite its legitimate uses, cryptocurrency’s untraceable payment nature has raised concerns around money laundering and illicit trade, driving regulatory scrutiny. Quinten Epting joined MUO in 2024 to share his expertise in artificial intelligence, task automation, and cybersecurity. He has previously contributed to Overt Operator, writing numerous OSINT-focused news stories that spotlight emerging cyber threats and pressing security challenges.

Step 4: Access I2P Sites (Eepsites)
However, effectiveness comes down to how well the tool aligns with your risk profile and operational needs. These platforms sell counterfeit or forged documents, including passports, IDs, driver’s licenses, and other official papers. They cater to criminals or individuals seeking to commit identity fraud or avoid legal scrutiny. These services are used to obfuscate the origins of cryptocurrency transactions, making it harder to trace them.
Tor Over VPN
So, you risk being flagged or investigated for visiting certain sites, even without criminal intent. The dark web is a hidden part of the web that is not indexed by traditional search engines like Google and requires specialized software to access. To find what you’re looking for, you may need to try multiple search engines or visit directories of trusted .onion links.
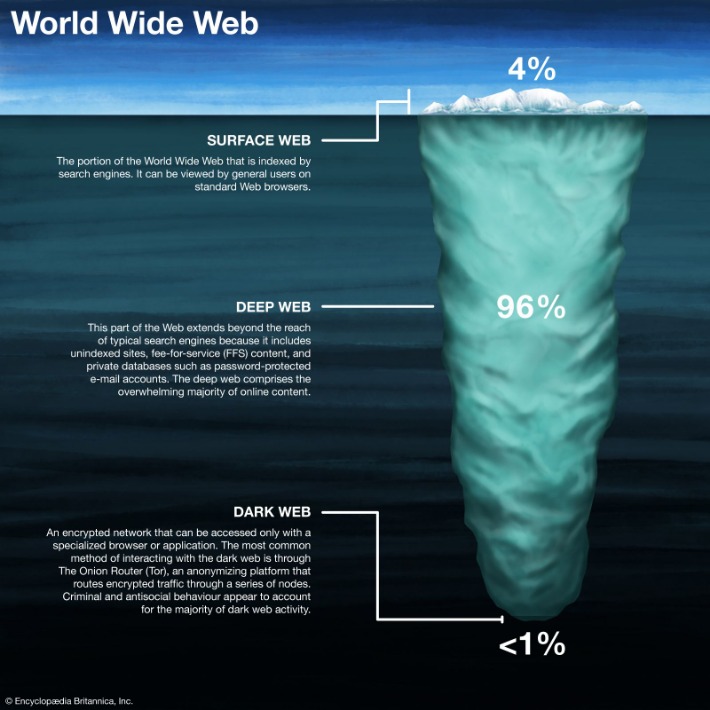
- The deep web is made up of content that search engines such as Google do not index.
- While the dark web itself isn’t illegal, several laws come into play depending on what’s being done.
- Many sites on the dark web are scams, and some host illegal content.
- Since their deadline wasn’t met for the closure of the sites a month later, the Impact team ascended to the dark web, where they started to publish the data.
- There are all sorts of threats on the dark web, and it’s all but impossible to verify whether a file is legitimate, so you’re likely to inadvertently download malware to your device.
Though a large volume of traffic visits on the open web every day, it only represents 4% of the content on the internet. If you carefully follow the six tips we have provided, you will be well on your way to accessing the dark web safely, securely, and anonymously. There will also be risks, but as long as you stay vigilant, you should not encounter issues. A large portion of activities on the dark web involve illegal content, transactions, or services. Simply accessing certain sites or engaging with the wrong links could implicate you in criminal investigations.

Cybercriminals often disguise harmful files as legitimate downloads, making it easy to get tricked. These search engines can help you discover .onion sites related to your interests. However, note that dark web search engines don’t index as many sites as regular search engines, so results can sometimes be limited or outdated.
Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top. DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web.

Is It Illegal To Visit And Use Dark Websites?
Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories. Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor. This internet space can be dangerous but you can safely get on it by using a VPN and then connecting to Tor. Our experience has shown that this is the #1 way of doing things without risking your privacy.

The affiliates distribute the ransomware packages through the dark web. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid. This is an extra precaution that can protect your device from savvy hackers looking for any opening that presents itself. Once you’ve chosen a VPN provider and have successfully set up your account, you’re ready to start looking at overlay networks. The US government created the dark web to help its spies communicate and exchange information securely. The Onion Router (Tor) also made the technology available in 2002.



