
You can use Tor without the browser, but the Tor Browser is the most popular and user-friendly way people interact with the protocol. For a limited time, new users who purchase any plan can claim 25% off their first order. The user will have the discount automatically applied after they click on it and check out. This guide dives deep into Tor, explaining how it works, its pros and cons, and how to utilize it to protect your online privacy. Here are some top tips for recognizing whether a service on the dark web is a scam or legitimate.
PRIVACY ALERT: Websites You Visit Can See These Details About You:
You can use third-party tools like Bleach Bit to completely wipe temporary files if you want to go the extra mile for security. After clearing the temporary files, reboot your computer to end any background processes that might still be running after closing the browser. You can get a VPN like NordVPN or ExpressVPN which have leak protection built in. You should also check that the VPN also features WireGuard protocol which is faster and more secure compared to older options like IPSec or OpenVPN.
How To Access The Dark Web On An IPhone
- Its competitive pricing ensures that robust privacy protection is as affordable as a cup of coffee.
- In fact, journalists, privacy advocates and academics use it every day to protect their identities and get to material that has not been blocked.
- As such, you should exercise caution when accessing any unofficial dark websites.
- This hidden part of the web carries several illegal activities, including drug and weapon dealing, pornography, private data, and more.
- The good news is that the BBC Onion site is an international edition.
Though most volunteers mean well, others are malicious actors and surveillance agencies. The worst part of the network is that you don’t have control over the nodes your traffic is routed through. There are no laws restricting access to websites on the dark web. However, using the dark web for illegal activity can be a criminal offense. After all, some websites on the deep web are like those on the open internet, except that they are hidden behind a paywall or protected via passwords to limit access. The dark web is a controversial part of the internet, famous for being a hotbed for illegal and criminal activity.
Illegal Streaming Sites
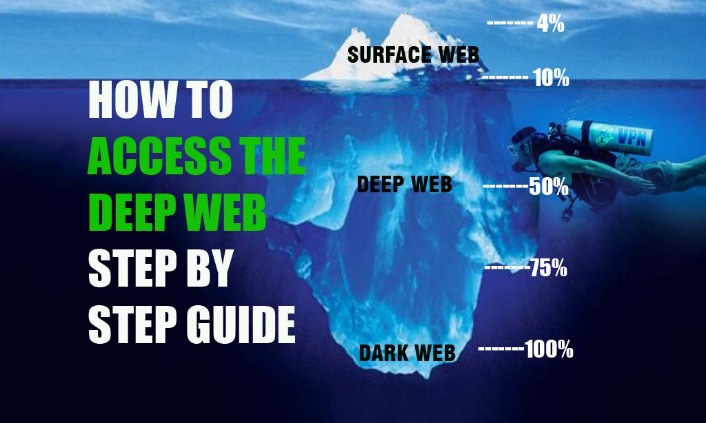
By following these tips, individuals can enhance their safety and privacy while exploring the Dark Web. The dark web is made up of a variety of different overlay networks and accounts for somewhere between 5-6% of the overall internet. It allows users to buy and sell, browse, and communicate with nearly complete anonymity.
Method II – VPN Over Tor
Taking the necessary precautions makes tracing your activities on the dark web difficult. For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities.
Tips For Accessing The Dark Web
If you want to observe the lawless sides of the internet from afar, check out YouTube videos of dark web explorations, like this one from John Hammond, to satisfy your curiosity. In this way, your browsing experience is made as anonymous as possible – if someone was ‘watching’ you, so to speak, all they’d be able to see is that you’re using Tor. For information about this, check out our guide on how to get on the dark web. To access the Dark Web, you have to use a browser called Tor, also known as The Onion Router.

How To Access The Dark Web Safely: Step-By-Step
- It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security.
- Tor isn’t available for iOS due to Apple’s restrictions, but you can still access the dark web on your iPhone using the Onion Browser, which is from the Tor Project.
- It encrypts your traffic at the entry node and changes your IP address.
- Accessing the Dark Web, a part of the web that isn’t indexed by standard search engines, is not illegal in most countries.
- If you discover your data on the dark web, act quickly to minimize the damage and report the incident to relevant authorities to ensure any necessary legal action is taken.
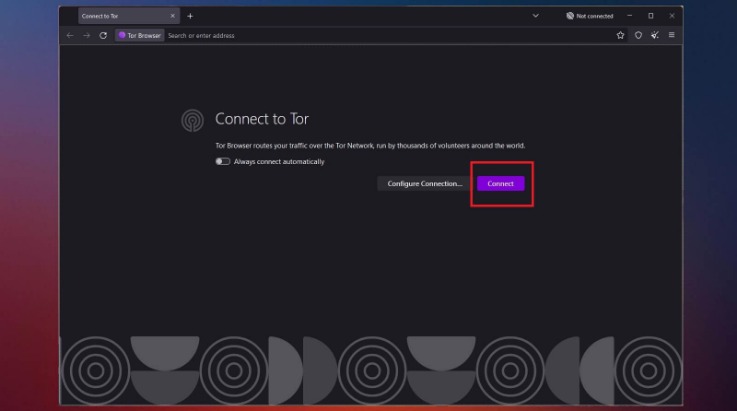
Using the Tor browser is simple, but knowing when to fire it up is more complicated. Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual. Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship.
If you fancy exploration, we’ve listed nine other options as well. Although it requires more work, it provides tech-savvy users with a more familiar interface with better security for accessing Tor through a proxy. It is made up of two virtual machines – a Gateway and a Workstation. All traffic must always go through the Tor network through the Gateway. This architecture protects your IP address even when the Workstation is before malware that may compromise it. To access the dark web, you must have specialized software, such as the Tor Browser.
The term ‘deep web’ doesn’t mean anything nefarious – it’s estimated to make up about 99% of the entire web. It refers to the unindexed web databases and other content that search engines can’t crawl through and catalog. The deep web is like an archive, containing an unsorted pile of websites and resources that are largely inaccessible to normal users. Now that you’re connected to Tor, you’ll need a dark web search engine to help you find .onion sites. Unlike regular websites, .onion sites have complex, hard-to-remember URLs that you can’t find using regular search engines like Google. No, simply accessing the dark web using Tor or other anonymizing browsers is not illegal.
Keep Your Data In The Dark — And Off The Dark Web
So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. We test each product thoroughly and give high marks to only the very best. We are independently owned and the opinions expressed here are our own.

Beyond this “surface web” is the deep web, and within the deep web is the dark web. Then, use data breach monitoring software to help find out if your personal data has leaked onto the dark web. The dark web refers to websites that are not on the regular internet but are instead hidden in a private network that is only accessible using specialized web browsers, such as the Tor Browser. Now that you understand the essentials of anonymous networks and how to prepare yourself for secure browsing, it’s time to explore the practical steps involved in accessing the Dark Web.
However, these names likely conjure up a scarier conception than the real definition of the dark web. Once the file is downloaded, run it to launch the installer and follow the prompt until the Tor browser is installed. Upon selecting the button for your operating system, you will be prompted to download the installer, which you should save to a folder. Upon opening the Tor website, you will be presented with various download options for the operating systems that Tor supports, including Windows, macOS, Linux, and Android. This information can be used to target ads and monitor your internet usage.



