
Users need to exercise caution when navigating this hidden realm of the internet. The Dark Web is not policed, meaning that malicious actors can easily take advantage of unsuspecting visitors. Therefore, understanding how to access the Dark Web safely using security measures is paramount. The primary purpose of accessing the dark web is anonymous browsing for activists and whistleblowers, but some people misuse this anonymity for illegal reasons. It is where the dark web becomes dangerous, and with no regulations, it becomes riskier to access without using a protective tool.
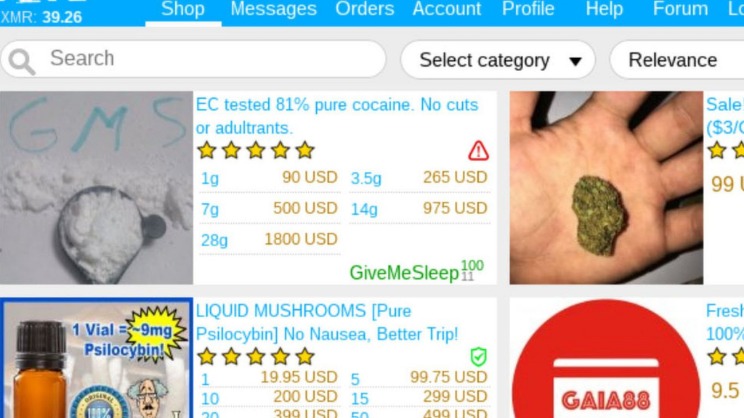
- The dark net is not quite as lucrative as it used to be and the prices for most of these items or services have gone down in recent years.
- You don’t need special tools or a special browser like you need to access the dark web (more about that later).
- Tor is slow, and it may attract unwanted attention from your government or ISP.
- If you log into personal accounts on the dark web or visit websites with tracking scripts, then your activity may be tracked.
- But it can’t stop you from entering personal information on websites to say where you are.
Browsing the dark web is riskier than browsing the surface web because it’s usually difficult to assess website safety. And without experience deciphering trustworthy dark web sites, it’s easy to fall prey to dangerous cybercriminals. Many of these services are legal and legitimate, but they can host illegal content or activity.
App Support
He strives to make complex cybersecurity topics accessible and understandable to the broadest audiences. In his spare time, Michael likes writing fiction, reading murder mystery novels, and spending time with his family. A lot of the user data that gets stolen or leaked from big platforms ends up on the dark web, where users buy, sell, and exchange it among themselves.
There are countries where access to the dark web is restricted by the government. For example, China blocks the Tor network IP addresses using the “Great Firewall”, and the Russian government has urged Internet Service Providers to block access to the Tor network. An escrow may be a special service and supported by a shadow platform, or a third party disinterested in the results of the transaction. Note, however, that on the dark web nothing eliminates the risk of being scammed with 100% probability.
How Can I Ensure My Privacy While Browsing Dark Web Links On Android?
Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. I2P can only be used to access hidden sites that are only available on the I2P network. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail.
Which Is The Best Free VPN For Tor?
Therefore, you should use a reliable VPN to hide your identity and create a safe cloud while entering into the dark world. This guide covers everything you need to know on accessing the dark web via your iPhone safely and anonymously. It’s also important to note that smartphones, in general, aren’t the most privacy-friendly devices (think GPS tracking) and have plenty of vulnerabilities that can be exploited. Continue reading to learn how to access the dark web on phone without compromising your privacy and security.
Marketplaces reminiscent of regular e-commerce websites, including the infamous Silk Road, thrive within its hidden corners. These platforms require specialized software for access and rely on cryptocurrencies for transactions. The anonymous nature of the dark web also attracts criminals engaged in heinous activities such as distributing child pornography. Dark web links, often referred to as “.onion” sites, are part of a hidden network that standard search engines can’t access. These sites are infamous for hosting illicit content, but many serve legitimate purposes, such as providing information in censorship-heavy regions or secure communication channels.

Using Tor Browser FAQs
Despite the presence of illegal marketplaces and the trading of sensitive information, the dark web also offers a place for anonymous communication, social networks, and lawful content. Before diving into the world of the Dark Web, it’s crucial to address the legality and safety concerns. While the Dark Web itself is not illegal, it does provide a platform for illegal activities to take place. Additionally, navigating the Dark Web comes with inherent security risks, as malicious actors may be lurking, attempting to compromise your privacy and steal sensitive information.
Reuters, Fox, NBC, CNN – all of them keep open dark web channels to receive anonymous tips from whistleblowers. People mostly use it for covert communication, anonymous tips submission, and stuff like that. Chill, because nobody will ever find a record of you ever fiddling around the darknet.
More On How To Stay Safe On The Dark Web
Your download and upload speeds may be slower, but that is the tradeoff for secure Internet browsing. To access the dark net and Tor using Brave, open the browser, choose the hamburger icon from the top toolbar, and select Private window with Tor. You will be connected to the Tor network, and then you can open onion websites and obfuscate your network activity.
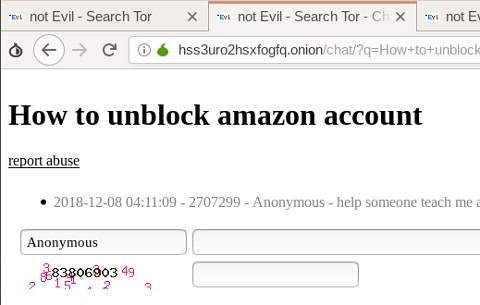
- Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia.
- Unlike the open web, these sites aren’t really worried about being found by on-page SEO tools like web crawlers.
- Its main appeal is that it offers more privacy and supports legacy Firefox add-ons.
- The Dark Web is known for its anonymity and the presence of unregulated content, which can include malicious software and various cyber threats.
- The dark web — aka, the deep web — is the second layer of the internet, which is not indexed by search engines.
Accessing The Dark Web On Android
For more information, read more about the most secure email service providers in my other post. So, once you’ve activated your VPN and your privacy is secured, it’s time to visit Tor’s official download page. It’s impossible to access the dark web with a regular browser like Chrome or Safari. So, to get into the Tor network, follow the steps I’ve listed below.
Anonymity is powerful with Tor and the framework of the dark web, but it is not infallible. This setup is easy to configure, and you don’t need any special settings or features. Just turn on your VPN, wait for the connection to stabilize, and launch Tor. Your internet activity is still subject to exit node risks, so always use HTTPS and avoid entering any personal information on unencrypted sites.
This adds an extra layer of security by masking your IP address and encrypting your connection. To improve your security, always use a VPN, configure your Tor Browser to the highest security settings, and avoid downloading files or providing personal information. It’s important to use a reliable VPN like Forest VPN, avoid sharing personal information, and stick to legal sites to enhance your security while exploring the Dark Web. However, engaging in certain activities, such as purchasing illegal goods or services, is against the law.
Thus, the dark web version of Facebook is there for bypassing censorship, not for gaining anonymity on the social media platform. On the other hand, those stats reveal that around 40% of the dark web is not actually illegal. The dark web is a part of the deep web that can be accessed anonymously using Tor browser. It is concealed from the clearnet (the part of the internet where you visit YouTube and Twitter) using encryption, and it allows web developers to publish websites anonymously. Whether you are accessing your email account, private backups, or your credit card statements, that data is stored on the deep web.
Can I Access The Dark Web Without Tor?
The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. However, this does not provide any extra security for your device or information. One of the great things about Tor is that it can be used to access both the dark and surface web. Just note that although you’ll be anonymous, you won’t have the speed or convenience of a direct connection, and some sites might block you outright. Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites. Obviously, finding these .onion websites is the first challenge, as they won’t show up in Google search results.
However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Using Tor is especially helpful in countries where authoritarian governments censor the internet, preventing citizens from accessing news outside their country. Your traffic is relayed and encrypted three times as it passes over the Tor network.
These search engines can help you discover .onion sites related to your interests. However, note that dark web search engines don’t index as many sites as regular search engines, so results can sometimes be limited or outdated. While VPN over Tor is a bit more complicated to set up, it protects you against malicious exit nodes. All data is routed from the exit node through a secure VPN connection. This prevents the node operator from detecting your IP address or from finding out any other information.
It’s worth noting that using a VPN can slightly slow down your internet connection due to the encryption process. However, the added security and privacy benefits far outweigh the minor inconvenience. Tor over VPN means you will first connect to the VPN and then to the Tor browser. The VPN encryption will prevent snooping eyes from seeing the Tor entry nodes that can’t see your IP address and hide Tor activity from your ISP. Accessing the dark web through your phone is much more dangerous than accessing it through a desktop or laptop, primarily because cell phones are personal diaries.



