This information can be used to target ads and monitor your internet usage. Despite these privacy concerns, Facebook has become a critical place for communicating and expressing opinions. You can head over to Archive Today to look at snapshots taken by other users. Alternatively, you can take a snapshot of a web page that you consider important and want to ensure is archived for freedom of information purposes. The great thing about sharing via the Dark Web on SecureDrop is that users can do so without fear of persecution and without the possibility of being tracked down and punished.
September’s Top VPN Discounts
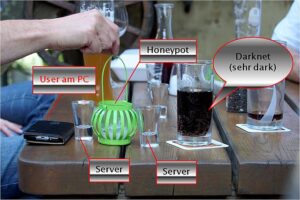
The Tor network is designed to provide you with privacy and anonymity. That said, most experts agree that at least some nodes on the Tor network have been compromised by intelligence agencies like the CIA and the NSA. First, check out our beginner’s guide on how to use Tor, then come back when you’re ready to get started. Hiddenwiki.pw is not liable for any loss or damage incurred as a result of using the above links. The rest of the wiki also offered links to sites hosting nudity, including child pornography and abuse images. If you suspect your data has been compromised, consider running a dark web scan to check for any leaks and report any instances of identity theft or fraud to the appropriate authorities.
FAQs About Dark Web Websites
Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to “join” your transactions with others to increase your anonymity. Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Your IP is still being revealed to one of the nodes in the onion, meaning your activity and identity can be unmasked. Since academic research is often fenced off behind paywalls, Sci-Hub aims to democratize knowledge by allowing people to see publicly-funded research for free. This means that using the dark web may attract attention from your ISP or even law enforcement.
Maltego + Darknet Plugins
A single wrong click could lead to a scam, malware infection, or even a stolen crypto wallet. Fortunately, there are trusted ways to verify whether a .onion link is legitimate. Always double-check URLs using platforms like dark.fail or onion.live, and never trust a site just because it looks professional. Set Tor Browser’s security level to “Safest” for critical dark web activity. This disables potentially dangerous features like JavaScript that could reveal your identity.
Best Onion Sites By Category
This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls.
Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. The Dark Web Index is a powerful tool for accessing hidden services, but staying informed about risks is crucial. By following these guidelines, you can explore the Dark Web securely and efficiently. Please be aware that accessing and using .onion sites comes with risks and legal implications. Use these resources responsibly and be cautious of potential security threats.
Proton also offers other security tools besides ProtonMail, such as Proton Drive, Proton Pass, Proton Calendar, and Proton VPN. Onion.name is a dark web resource that helps make sense of the mess of letters and symbols that usually form the darknet sites. It has a vast library of over 1.5 billion indexed pages that lets you find whatever you are looking for. However, the threat of clicking on the wrong link always remains, so be cautious while you use it. To provide freedom of speech and keep journalism a strong pillar of the economy, the BBC made this Tor mirror. It helps people anonymously use the BBC website without restrictions.
Facebook Onion Site

Safe browsing on the Hidden Wiki requires a combination of technical precautions and behavioral discipline. Always access the Hidden Wiki through the official Tor Browser, never via a standard browser. Disable JavaScript and other potentially risky browser features unless necessary, as they can be exploited to reveal your identity.
- Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions.
- Feather is a free and open source Monero wallet available on most major computer platforms.
- It’s a hidden collective of sites that you could only access through a special browser.
- It’s a wallet, explorer service, not a dark web marketplace itself, but still a helpful resource.
- These concerns are valid because using Facebook undoubtedly exposes users to some of the highest levels of surveillance capitalism anywhere on the web.
What Are The Best Onion Sites
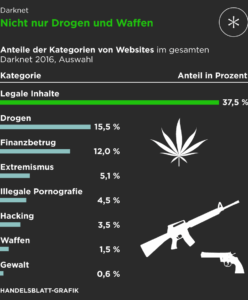
But anything that’s against the law on the regular web or offline is also illegal on the dark web. This includes buying or selling illicit goods, illegal transactions, and downloading copyrighted material. Onion sites are websites on the dark web that use the “.onion” top-level domain instead of “.com,” “.net,” “.gov,” etc. Onion sites use The Onion Router (Tor) software to encrypt their connections and enable anonymous communication.
It’s a thoughtfully curated directory that filters out dead links, scams, and outdated sites. However, there are many websites engaged in highly illegal or harmful activity. Unlike traditional websites, the Hidden Wiki was hosted as a Tor hidden service (.onion domain), ensuring anonymity for both its operators and users. Both DuckDuckGo and Ahmia are safe choices for finding Tor Browser links without being tracked. Any onion websites you visit from these search engines is another story.
When delving into the dark web, maintaining stringent security and preserving your anonymity aren’t just advisable—they’re essential. Threats here range from malicious actors looking to harvest your personal data to hidden exploits designed to compromise your system. A careless misstep can lead to exposure, malware infection, or worse. To protect yourself, it’s crucial to combine multiple security layers, stay vigilant, and adopt best practices tailored for the hidden corners of the internet.
The Role Of Forest VPN

The search engine has indexed over 400,000 pages, and you can ask it to match your exact search term. You can easily find what you are looking for, even links to hidden dark web rooms. With ZeroBin, you can easily exchange encrypted messages within the dark web. With 256-bit AES encryption, this platform enforces its two-fold service of secure messaging and zero logs of your activity.
F Onion Websites: Between Anonymity And Risks
(b) is the deep web, which consists of sites that require a login to access like email accounts, banking portals, and subscription services. And (c) is the dark web, which is the part of the deep web that isn’t indexed by search engines and requires special tools like Tor Browser to access. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
It was initially created to provide additional security and eliminate cryptocurrency theft. It’s a wallet, explorer service, not a dark web marketplace itself, but still a helpful resource. While this is not much compared to standard email services, it is enough for PGP-encrypted messages.