These are communities stretched across dark and surface web forums which develop shared tutorials and help one...
Deaths involving fentanyl nearly doubled from the previous year’s rate in 2014, 2015, and 2016 2. To...
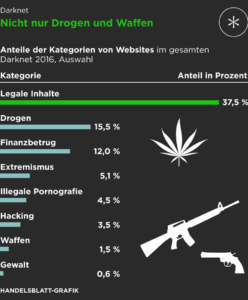
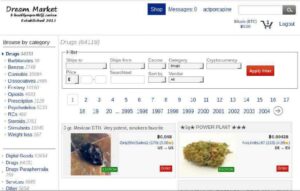
Sales are hard to measure with certainty on darknet markets, but by checking customer feedback with specialist...
For example, the Monero cryptocurrency, which uses a privacy-focused blockchain, has been popular on the Darkweb due...
In 2025, the landscape of darknet markets has evolved significantly, offering users enhanced security, reliability, and a...
The darknet has become a cornerstone for secure and efficient drug trade, offering users unparalleled privacy and...
It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be...
Although discussions about ransomware are banned, multiple ransomware-as-a-service (RaaS) operators are still active on the forum to...
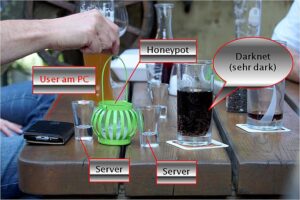
The law enforcement community needs to develop new ways to monitor illegal drug trades in the Dark...
Many of these big markets are now engaged in cyber warfare, with vendors and operators attacking each...