In this volatile ecosystem, recognizing the dynamic nature of the dark web is half the battle. By acknowledging that services, communities, and security measures are in constant flux, you can better position yourself to respond effectively. Even if you’re using a private, anonymized crypto wallet, there are other ways your identity can be revealed—even if it’s something as simple as letting a personal detail slip in an instant message. However, there are plenty of legal and legitimate online activities that require privacy and anonymity. The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers.
Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage.

Just as you need the right tools to access the dark web, you also need the right protections to be able to stay safe on it. Before you go exploring the dark web, it’s crucial to recognize that it is much more dangerous than the surface web — and not just because of all the illegal activity happening on the dark web. Even if you’re a law-abiding citizen only looking to see what’s in the dark, hidden alleys of the internet, there are many dangers that can befall you. To safely access dark web websites, use the Tor browser along with a VPN for added security. Additionally, ensure your antivirus software is up-to-date and avoid clicking on unfamiliar links. The dark web refers to web pages that are not indexed by commonly used search engines.

Use Trusted Resources
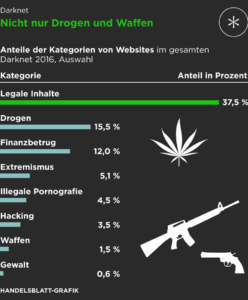
- The so-called “Dark Web” often conjures up images of hidden bazaars for illicit goods, secretive communication channels, and shadowy corners of the internet inaccessible through standard search engines.
- The dark web can be a very interesting place with some great websites to explore.
- This includes lucrative affiliate programs to attract technically skilled partners and tiered access enabling affiliates to pay for premium tools, zero-day exploits or access to pre-compromised networks.
- This makes it extremely hard for anyone to identify the source of the information or the user’s location.
- When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails.
- To enter this hidden world, users rely on the Tor browser, a specialized tool designed to keep web activity private by bouncing it through a network of relays around the globe.
The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private. The Hidden Wiki is a comprehensive starting point for exploring verified dark web links. Unlike many imitators, this is the official Hidden Wiki that maintains a curated directory of legitimate .onion services. During my testing, I found its categorized index particularly helpful for discovering trustworthy sites across various topics. Simply put, onion sites are websites that are hosted on the Tor darknet that use the “.onion” top-level domain instead of “.com,” or “.gov” for example.
Privacy Tools And Services
Hidden Answers is an anonymous way to post your questions on any subject. The sharing of illegal pornography and discussion of illegal sex acts account for a significant portion of dark web traffic. The extent of the problem became clear in 2015, when the FBI shut down a dark web site on Tor named Playpen that hosted 23,000 sexually explicit images of minors. Onion sites are websites on the dark web that use the .onion domain.

Bitcoin allows for anonymous donations, making it easier for terrorists to fund their activities and purchase weaponry. In some cases, fraudulent websites claim to be used by terrorist organizations such as ISIL. With the current technology, cyber terrorists can exploit their weaknesses to carry out attacks.
Monitor System Resources
Since the organization behind it is independent, it’s fully user-supported and relies on donations to keep its site up and running. All of this underscores Riseup’s prioritization of users’ rights over business interests. So take this guide as you explore where to go on the Tor Browser without risking your online security.
Definitely yes, especially if this is your first time on the dark web. Hidden Wiki, although comprehensive, contains some very disturbing and very illegal info. Several dark web search engines allow people to explore this hidden part of the internet.
Legitimate Uses Of The Dark Web
Privacy-focused internet users who access onion sites may see greater anonymity while browsing or sharing sensitive information. These pages can also help circumvent some forms of government censorship. Dark web websites are pages that exist on a part of the internet that isn’t indexed by traditional search engines like Google. Also known as deep web sites, these pages typically have URLs ending in .onion and are only accessible through special software like the Tor Browser. While this filtering is intended to improve user safety, it can also prevent access to content that is relevant for research or dark web activity monitoring purposes. This search engine’s indexing is relatively shallow compared to other uncensored engines, meaning many dark web sites remain undiscovered or unlisted.
Best Onion Sites To Discover On The Dark Web In 2024
WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process.
Dark Web Chat/Social Networks
While strong encryption, VPNs, proxy servers, and hidden web addresses can all contribute to a more anonymized experience, there is no singular system available that is completely private and secure. First — and this is strongly recommended — you should install a Virtual Private Network (VPN). Also, you need to use a privacy-focused browser such as the Tor network to connect via nodes and proxy servers, which are more secure and aim to anonymize traffic requests. The Tor browser is able to access the special domain names, with the suffix .onion, used in the dark web.
You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. This isolates any potential malware and prevents cross-contamination with your personal data.

Password managers can help manage your credentials without compromising security. ProPublica is a non-profit, Pulitzer Prize-winning news outlet that focuses on abuses of power and issues of public trust. ProPublica’s investigative journalism can upset powerful interests, so the outlet joined the dark web to help their journalists and readers access their content anonymously.
Staying Safe On The Dark Web
There are other ways for spies, hackers or other adversaries to target Tor. Lewis points to the “first contact problem”, when an attacker spots when someone moves from non-private tools to private ones, noting it’s been used to identify whistleblowers. There are different levels of security in the browser that are worth considering. To review security settings, click on the onion logo in the top left and select “Security Settings”, which will bring up a slider offering a choice of the default of standard, or safer and safest. In “safer” mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won’t run automatically, you’ll have to click to play.