Similar to using a standard web browser to access the open web, the act of using Tor or a dark web browser to access the dark web is not illegal in and of itself. It is illegal to perform illegal acts on the dark web, regardless of the level of anonymity provided by the platform. The biggest differentiator between the deep and dark web is that dark web activity is made anonymous through a variety of encryption and routing techniques. Surfshark supports unlimited simultaneous connections to protect as many devices as possible.
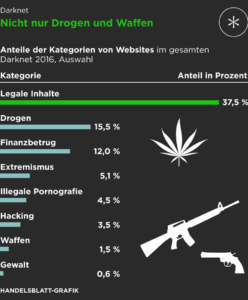
It also helps users bypass government restrictions to access censored information and services. Given its anonymous nature, the dark web is also used for illicit and even illegal purposes. These include the buying and selling of illegal drugs, weapons, passwords, and stolen identities, as well as the trading of illegal pornography and other potentially harmful materials. Several sites hosting illegal material have been discovered by government agencies and shut down in recent years, including Silk Road, AlphaBay, and Hansa. The dark web’s anonymity has also led to cybersecurity threats and various data breaches over the last few decades.
Learning About The Dark Web
Despite its negative reputation, not all activity on the dark web is malicious; some users rely on it as a tool for freedom of expression or to circumvent restrictions. These platforms provide services related to illegal activities, such as hacking tools, malware, ransomware, or services for hire (e.g., DDoS attacks, identity theft). Some sites might offer tutorials or guides for aspiring cybercriminals.
The visitor has to use the same encryption tool as the site and – crucially – know where to find the site, in order to type in the URL and visit. Your data is almost certainly in the deep internet – and you can only hope that it stays there. This would include doctor records on the hospital intranet or even school records. Your data is being stored, and you can only hope that the companies are keeping it according to GDPR standards, which requires them to keep it safe via various methods like using encryption. While ad blockers can prevent most harmful links from loading, you should also take steps to protect yourself from malware to keep your data safe from hackers and scammers. Whilst using Tor isn’t illegal, the encrypted data packets it uses make it fairly easy to detect.
Hacking And Cybercrime Tools
The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals. Onion links have no regular domain names registered under the domain name registry. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser.
How To Access The Dark Web Using Tor

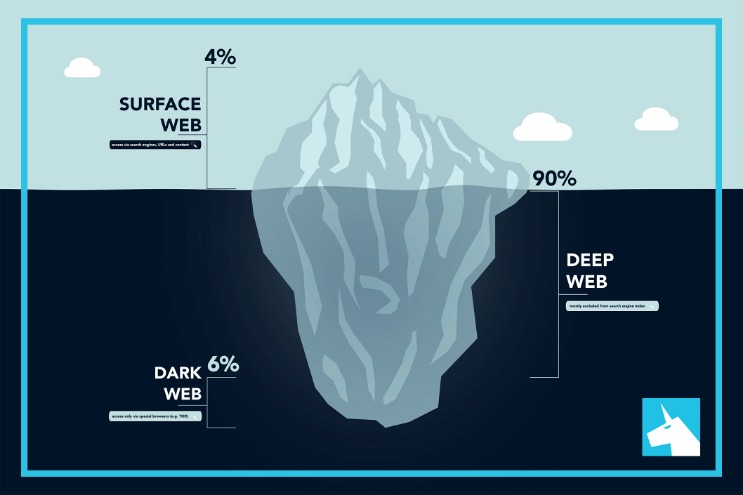
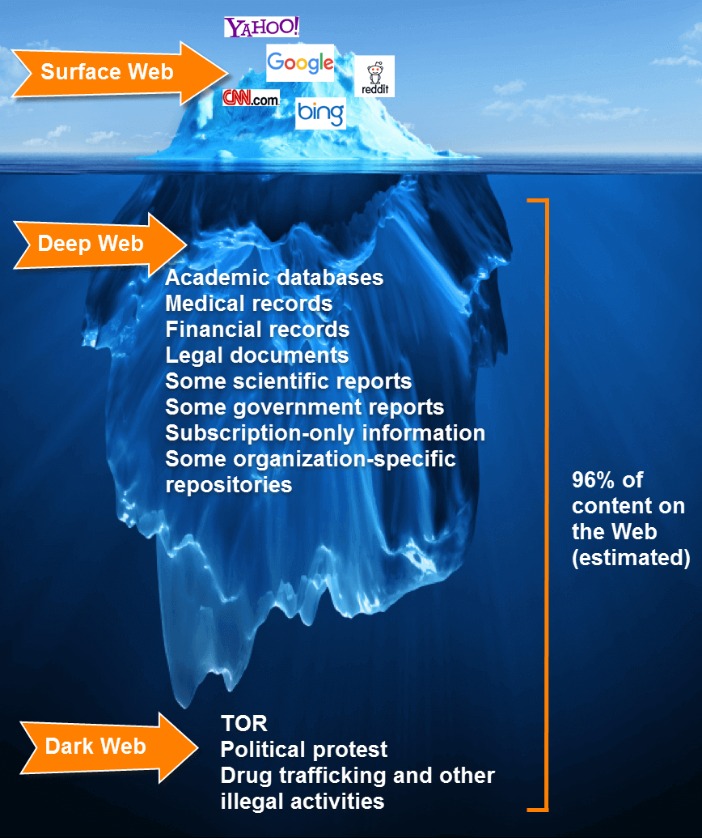
But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search. Typically, any reference to the visible web will be to common websites with a familiar internet domain extension.
How To Remain Safe When Using Darknet Browsers

By investing in dark web monitoring tools, training staff, and implementing cybersecurity best practices. Panda Security specializes in the development of endpoint security products and is part of the WatchGuard portfolio of IT security solutions. Initially focused on the development of antivirus software, the company has since expanded its line of business to advanced cyber-security services with technology for preventing cyber-crime. The dark web is full of links that can lead you to dangerous sites or trigger malware downloads. Visit links with caution, especially if they seem unfamiliar or suspicious.
- A VPN creates a secure connection between your computer and the internet, encrypting your data and hiding your IP address, making it difficult for anyone to track your online activity.
- Finding information on the dark web can be challenging due to the complex and constantly changing nature of dark web addresses, which often consist of random numbers and letters.
- Haystak is a dark web browser that offers better filtering features that help users refine their search results, enabling them to locate exactly what they need.
- It collects data from the public Tor network and archives historical data of the Tor ecosystem.
- The hidden nature of the dark web has earned it the nicknames black web and underground internet.
- One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online.
US Cybersecurity Laws Related To The Dark Web
Some hackers offer ransomware as a service (RaaS), where cybercriminals can “rent” a strain of ransomware from its creator in exchange for a fee or a percentage of their ransom payments. Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data. Some of these are well-known, established threats that circulate in this nook of the web. However, others may be taking advantage of the dark web’s reputation to trick users out of large sums of money. Also, some users on the dark web may attempt phishing scams to steal your identity or personal information for extortion.
Where it’s legal, accessing the dark web can serve legitimate purposes for threat analysts, privacy advocates, and security practitioners. To properly peel back the internet’s layers, you need a tool that provides layers of encryption to hide your activity. Tor Browser is a tool created and maintained by a non-profit privacy group, and it uses onion routing to repeatedly encrypt data and route it several times before it gets to its expected destination. Those layers of encryption and routing activity help to anonymize your movements. Keep in mind though, even the Tor browser isn’t an infallible privacy solution. You can still be tracked at network entry and exit nodes, as indicated by reports that police identified Tor users by surveilling data centers.

Ransomware leak sites showcase attackers’ successes, publishing sample files, threats of full data dumps as well as names and stolen data of victim organizations that refuse to pay. TOR is the most popular way to access the Dark Web while shielding a user’s location. Also known as The Onion Router, TOR enables users to browse the Internet, including the Dark Web, anonymously. It bounces traffic through several servers before delivering it to its destination, making it harder to track a user’s activity or location. When venturing into the dark web, it is crucial to prioritize safety by educating oneself about potential risks and employing robust security measures to protect data and maintain privacy. The dark web’s hazards include many risks, related to network breaches or data compromises.
Privacy-focused Search Engines
In this section, we’ll delve into the darker side of the dark web and explore the various illicit activities that take place there. Private Internet Access has 10+ years of experience leading the VPN industry. With a strict no-logs policy, world-class server infrastructure, and transparent open-source software, PIA prioritizes your online privacy, security, and freedom above all else.
Use Encrypted Communication Tools
The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article). Though people usually think of dark websites as the wrong online place, that’s not the complete truth. Although the underground internet world is rife with everything bad, it also hosts positive elements. While strong encryption, VPNs, proxy servers, and hidden web addresses can all contribute to a more anonymized experience, there is no singular system available that is completely private and secure. VPNs are also used for accessing geo-locked content hosted by streaming services.
Online Degrees
Zero-interaction chatbots on illicit forums can guide apprentices via malware development, creating dynamic, adversarial training environments. AI-as-a-service (AIaaS) platforms offer many of these capabilities that lower the barriers for cybercriminals to carry out these attacks. Generative AI is being used to fabricate synthetic identities, including deepfake voices, forged credentials, and AI-generated backstories. “Identity fraud is enhanced through synthetic persona generation and deepfakes, aiding criminals in bypassing know your customer (KYC) and biometric checks,” says Kroll’s Currie. “Threat actors are wanting to drive focus on their own brand names to gain more notoriety for themselves, such as the regular launching of new ransomware group brand names and leak sites,” says Carroll. To help understand the changing dynamics, here’s what CISOs need to know about the trade of stolen information, new marketplaces, the availability of malicious tools, and the impact of AI on the dark web.
Can The Government Track You On The Dark Web?
Hacker services against banks and other financial institutions are offered there. Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito.
While it may seem vast, the surface web actually makes up only a small fraction of the entire web. Think of it as the glossy shop windows of the internet — what you see is only what’s on display, neatly categorized and searchable. Again, these hacking forums sound intriguing but are filled with people who scam and lie for a living. As such, we will not discuss the full range of illicit and extremist content on the dark web. Read on to find out what you’ll find on the dark web—and if it’s worth visiting at all.